
Let’s look at what actually threatens users. Accessing it to buy drugs or stolen data will get you arrested. Accessing the dark web to bypass censorship is legal. ProtonMail operates on Tor to protect privacy and combat censorship. They were arrested for buying drugs, running illegal marketplaces, and selling weapons. What gets you arrested is what you do once you’re there.
Advantages Of VPN Over Tor
Octo Browser stands out as a highly efficient tool for managing multiple online identities. Specialized dark web browsers provide the necessary layers of encryption and anonymity. Standard web browsers like Chrome or Firefox won't suffice to access the dark web.
A government agency or a hacker can easily track where you had been and what you had been doing on the internet. Websites generally track you for providing you with a personalized experience. Google has been using this technique for a long time to improve its advertisement network and eventually make more money. All you require to do is simply type in your query in the search engine and press enter. You might already be keen enough to know how the dark web browsers work for anonymous web surfing.
- Yes, both platforms have official .onion versions accessible via Tor.
- This is partly due to their ephemeral nature and the privacy-centric design of the Tor network.
- It is legal to use anonymized browsers such as Tor and I2P.
- However, you can find legitimate content and activities here, too.
- Some countries allow people to use a deep web browser (such as Tor Browser) to do a lot of things online, but understandably, they don’t support people in doing things that are illegal with the tools.
A Quick Guide On How To Use A VPN With Tor
The dark web economy generates $1.5 billion annually from stolen data and illegal products (EarthWeb). Many dark web sites serve malware disguised as legitimate tools or leaked data. Without it, your ISP sees you’re using Tor and can flag your account for monitoring or block Tor entirely. VPN encrypts your traffic before it enters the Tor network.
Are There Alternatives To Tor Browser For Dark Web Access?
These browsers apply multi-layered encryption, route traffic through multiple nodes, and automatically erase browsing traces. Some websites claim to offer “online dark web access” through proxies or Tor gateways, but these come with risks. However, it’s not as secure as the full Tor Browser, since it doesn’t route all system traffic through Tor and may leak data if misused. These websites often use the .onion domain and are hidden from traditional search engines like Google or Bing. While Tor does provide excellent anonymity, routing your traffic across multiple relays, an observer outside of Tor (your ISP, for example) can see that you are connecting to the Tor network. You can use Brave’s Tor integration to add a basic layer of anonymity for general browsing, but don’t rely on it as a high-security option for accessing the dark web.
How Is Tor Different From A VPN Or Proxy Server?
As Tor is encrypted by default, most dark web websites don’t use this same certification. The “S” in HTTPS stands for secure, and signifies that a website has an SSL Certificate and encrypts data traveling between your device and a website. Safer disables website features that often cause security issues, but this also causes some sites to lose functionality. But Tor does have some vulnerabilities, and as with any browser, Tor users remain vulnerable to online threats, ranging from malware to phishing scams. If you’re interested in anonymous browsing, first check whether Tor, or even VPNs, are legal in your country.
Method II – VPN Over Tor
Tor Browser is primarily used as a method of anonymous browsing. Though Tor is slower, the process of rerouting data through nodes makes it more difficult to trace your activity back to you. In addition, Tor and VPNs take different approaches to rerouting data.
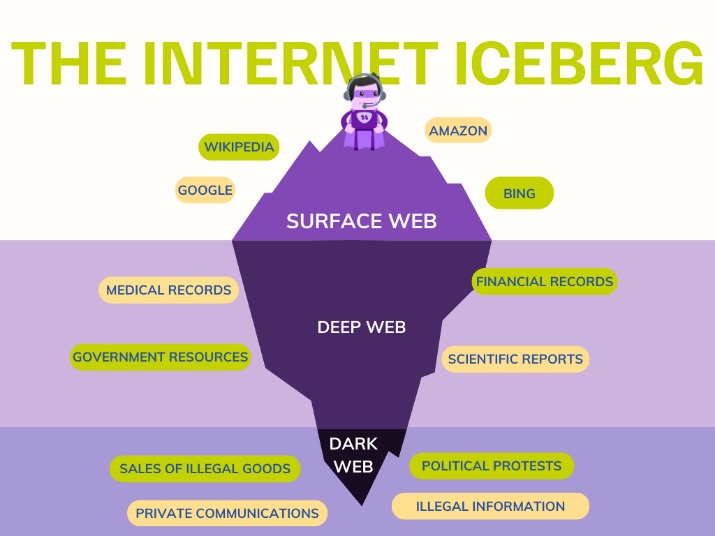
Ahmia sets out to be the “premier” search engine for sites on the Tor network. It’s extremely capable at hiding your IP address from traffic analysis or network surveillance. The deep web contains mostly benign websites that aren’t on the surface web where browsers like Google can find them.
It is not only not designed for browsing the web, but it is an anonymous layer of communication for email, messaging, team collaboration, file sharing, or whatever you are working on. I2P, or The Invisible Internet Project, is an anonymity tool that is entirely different one when you compare it to Tor. The simple work that the Tor Browser does is to hide the people using it from monitoring eyes and allow them to open the dark web safely. Apart from being the pathway into the hidden web, you can also use the browser for other things you want to do online without anyone noticing you at all.
What To Do If You See Something Illegal

ZeroBin is a wonderful way to share the content you get from dark web resources. Blockchain even has an HTTPS security certificate for even better protection. It was initially created to provide additional security and eliminate cryptocurrency theft. Blockchain.info (now Blockchain.com) is a popular cryptocurrency wallet and blockchain explorer service (one of the first sites to launch on the dark web). The Mailpile .onion site can download information anonymously from any server or web service like Gravatar.
Tor Browser Developer Tools
Although they can’t see your browsing activity or Tor-encrypted data, your ISP can still see that you’re using Tor. Simply put, onion routing is how Tor works, and how dark web websites can be browsed without anyone except you knowing. Tor uses onion routing to encrypt and reroute web traffic through Tor’s onion network. Because Tor hides browsing activity and blocks tracking, it’s used by whistleblowers, journalists, and others who want to protect their privacy online. However, using the Tor browser for illegal acts is possible since the network has increased anonymity.
Quick Comparison: Best Anonymous Dark Web Browsers
Picture the internet like an iceberg. However, their use for any illegal purpose or malicious activity is strictly prohibited almost everywhere worldwide. We’ve listed the 10 best dark web browsers for 2025.
- Here’s a step-by-step guide to setting up Tails on a USB thumb drive and using it to access Tor.
- And while both Tor and VPNs provide security and privacy, I think VPNs are better because Tor has some security issues.
- If you are browsing Tor’s onion sites, you should tread carefully and only visit reputable ones.
- Even in locations where Tor is legal, strict Internet use regulation laws in some regions may make accessing specific dark web content legally risky.
- Tor's hidden services have .onion domain names, which is why some people call Tor “the onion browser.”
- If someone visits two different sites that use the same tracking system, they'd normally be followed across both.
A key difference between Tor and a VPN is that a VPN’s network is operated by a central service provider, while the Tor network is decentralized and run by volunteers. Using a proxy server in combination with Tor Browser can help to hide the fact that you’ve connected to the dark web, but it won’t confer any additional cybersecurity benefits. A proxy server acts as an intermediary between you and host services, while Tor is an encrypted network of decentralized servers. You can also be identified if you log into an online account or provide personal details to a website while using Tor. Tor Browser is anonymous in terms of hiding your location and browsing activity — but there are limits.



