Despite its name, the marketplace operates primarily in English and serves a global audience. Established in 2019, Russian Market is a well-known and highly regarded data store on the dark web, specializing in the sale of PII and various forms of stolen data. It is a hub for financial cybercrime and offers a wide range of illicit services and stolen data that cater to sophisticated cybercriminals. Valued at approximately $15 million, Abacus Market is one of the most lucrative platforms in the dark web ecosystem.
Darknet Market
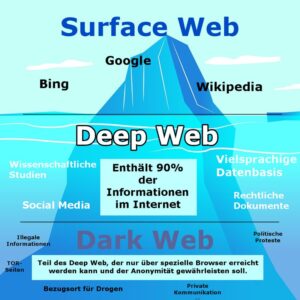
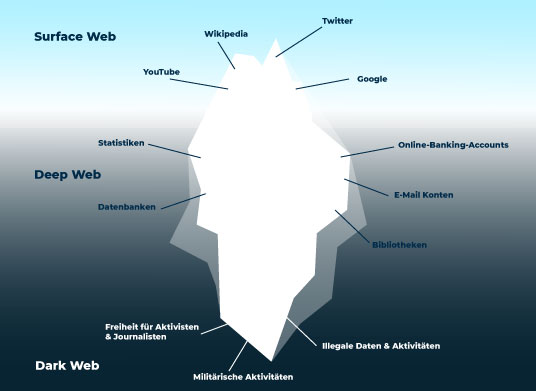
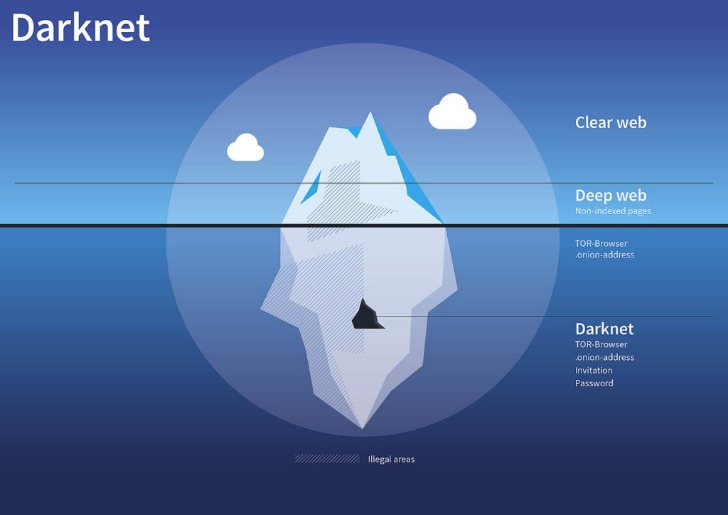
- This process creates an encrypted circuit through multiple volunteer-operated servers, obscuring the user's original IP address and location.
- Accessing the Nexus shop requires obtaining its official onion address, which is typically disseminated through dedicated verification channels and forums.
- This resource is systematically updated by the platform's administrators, ensuring that users are never more than one click away from a valid access point.
- Accessing the marketplace requires using its official onion links or verified mirrors, which are designed to provide stable and secure entry points.
- For maximum security, this process is often combined with a VPN (Virtual Private Network), adding an extra encryption layer before the connection even enters the Tor network.
- This commitment to a frictionless user experience makes Nexus a leading destination for efficient and straightforward transactions.
The market organizes everything clearly, more likely in an attempt to help newcomers (we should rather say criminals) find what they need easily. It stands as a reliable alternative to the defunct AlphaBay Market as it continues to position itself as the premier source for advanced privacy-focused digital commerce. During our tests for the research, we were able to register with a bogus email and a random username. It offers a wide range of goods and services with robust anti-DDoS protection (with military-grade security protocols) and no JavaScript, ensuring privacy and uptime.

Easy Access To Nexus With A Working Link
Markets often feature detailed product descriptions and laboratory analysis results, enabling consumers to make purchases based on verified information rather than uncertainty. The ability to access a wide variety of substances from different international sources allows for direct comparison of purity and price. This continuous adaptation creates a stable environment where commerce can proceed with a high degree of confidence for all parties involved. A critical component is the escrow system, which holds the buyer's cryptocurrency in a secure, third-party account until the product is received and confirmed. These integrated tools create a streamlined environment where transactions can be conducted with a high degree of confidence in the integrity of the process.

How Onion Addresses Keep Your Shopping Private

After the Biker DLC, players can now purchase buildings for illegal drugs and counterfeit products manufacture, and distribute them through a darknet website called "The Open Road" where law enforcement cannot be notified of the player's trade. A study based on a combination of listing scrapes and feedback to estimate sales volume by researchers at Carnegie Mellon University captured some of the best data. Examples include the sale of high-quality products with low risk for contamination (including lacing and cutting), vendor-tested products, sharing of trip reports, and online discussion of harm reduction practices.
The Smooth Operation Of Darknet Commerce
Each server, or node, in this chain peels away a single layer of encryption, similar to the layers of an onion, ensuring that no single point in the network possesses both the origin and the final destination of the data packet. The inherent properties of cryptocurrency provide a layer of financial privacy that is crucial for these environments, allowing for seamless and secure exchanges without the need for traditional, identifiable financial institutions. The Nexus Market has established itself by providing a stable platform with redundant access points, which minimizes downtime and protects against common connection issues. A reliable darknet URL is the first critical component for a secure transaction environment. These links are cryptographic addresses that resolve through the Tor network, ensuring user location and identity remain concealed.
Vendor profiles are central to this system, displaying detailed feedback ratings, sales history, and shipping policies. These sites have moved beyond basic functionality to offer a sophisticated and user-centric experience. This network of mirrors is not merely a convenience but a critical component for secure shopping.
These sites cater to cybercriminals seeking valuable data, such as credit card numbers, login credentials, and personal information. Telegram channels supplement traditional onion sites, blurring lines between the dark web sites and more mainstream communication tools. Dark Web Marketplaces continue to thrive as central hubs for these illicit transactions. Despite growing crackdowns from law enforcement agencies, the dark web remains a hotbed of criminal activity, offering everything from drugs to stolen data.
Ethical And Legal Boundaries In Monitoring Darknet Marketplaces
They seized Archetyp’s servers in the Netherlands, arrested the alleged 30 year old German admin in Barcelona, and targeted high volume vendors. Active from 2020 until June 2025, it amassed 600,000 registered users and 17,000+ listings. It specialized in narcotics fentanyl, heroin, cocaine, stolen financial data, fake documents, and even in house money laundering/mixing services. Unlike Western markets, Hydra was Russian language only and became the dominant hub for Eastern European and global cybercrime. By far the largest darknet market by volume was Hydra, launched in late 2015 in Russia. It supported 5,400 vendors and about 1.15 million customers worldwide.
What You Can Do With This Directory
The website allows visitors to view all the goods and services on display before they buy something. There’s also a search bar that you can use to search for any particular product or vendor. If any user is found not complying with the law, strict and immediate action will be taken against them. This site supports PGP encryption and two-factor authentication features. It allows you to buy and sell a wide range of products and services with a good user experience.
Dream Market Review – Best Darknet Marketplace
The architecture of modern darknet markets is designed for direct access to a comprehensive inventory. The focus on reliability, security, and ease of use demonstrates a maturation of the darknet marketplace model, ensuring that participants can engage in commerce with minimal friction. Access is safeguarded by secure onion links and URLs, which protect user identity and financial activity.
Its interface is engineered for clarity, presenting organized product and vendor lists that facilitate straightforward navigation and informed decision-making. This escrow model, powered by Bitcoin, builds trust between anonymous parties and secures the economic transaction against fraud. Transactions are recorded on a public ledger, the blockchain, but they are linked to cryptographic addresses rather than personal information, creating a layer of financial obfuscation. The reliability of a specific URL is paramount, as phishing sites with similar-looking addresses are a common threat designed to steal user credentials. To use these links, individuals employ the Tor Browser, which routes their connection through multiple volunteer-operated servers, obscuring the original IP address and the final destination.
The marketplace sells many things, including drugs, stolen data, and fake goods, using the Bitcoin, BitcoinCash and Monero cryptocurrencies. Accessing them may require .onion links and the Tor browser, but caution is advised due to legality and cybersecurity risks. Here are some of the now-defunct dark web markets that were notorious for cybercrime. WeTheNorth is a Canadian market established in 2021 that also serves international users. BidenCash’s rapid rise and focus on financial data make it a significant concern for cybersecurity professionals. Launched in 2023, STYX focuses on financial crime, providing stolen credit card data, hacked bank accounts and access to various cryptocurrency laundering tools.
The use of official onion links and PGP verification for all communications is standard practice, ensuring secure access and protecting user identities. In 2025, the leading darknet markets have refined their operational security and user interface design. The combination of a reliable platform, secure access via direct links, and a private payment system creates a robust framework for commerce. A market's presence on a verified darknet market list is a primary indicator of its stability and reliability, serving as a crucial vetting mechanism for users. Secure access to these platforms is achieved through verified onion links, which are regularly updated to prevent phishing and link rot. The ecosystem is supported by a collective commitment to security and discretion, making modern darknet marketplaces a viable and efficient channel for commerce.
Maintaining consistent access to a darknet market is a fundamental requirement for its operational success. The marketplace functions as a comprehensive online drug store, providing a vast catalog of substances. The platform's architecture is designed for stable performance, minimizing downtime and ensuring consistent access for its user base.
For enhanced anonymity, connecting to the Tor network via a Virtual Private Network (VPN) adds a critical extra layer of security, obscuring the user's origin point from the internet service provider. This system requires multiple cryptographic keys to authorize a transaction, protecting buyers from vendors who might not ship products and protecting vendors from fraudulent chargebacks. For enhanced security beyond the standard Tor configuration, connecting through a Virtual Private Network (VPN) adds an extra layer of encryption before the data even enters the Tor network, providing a more robust anonymity solution.