
Even if such sites were blocked from the regular open web, anyone using the Tor Browser could still access their email using the .onion addresses. Facebook offers an onion link to access their services, although you may find logging in difficult, as you’ll most likely appear to be signing in from a different location each time. While it is not flawless in protecting user privacy, it works well enough to give users much more privacy in where they go, the content accessed, and protecting their identity and location. This means content of such sites isn’t accessible to web crawlers.
While the dark web has search engines such as Ahmia that index some ".onion" websites, many hidden services are not indexed at all. A top-of-the-line VPN network that ensures maximum security while accessing dark sites online. Instead, users rely on dark web search engines like DuckDuckGo or directories, such as the Hidden Wiki and its offshoots, to find .onion websites.
I2P – The Invisible Internet
Thankfully, it allows you to connect unlimited devices, which will be useful when exploring the onion links with many devices. Surfshark is a budget-friendly VPN with robust security features. The VPN boasts bullet-proof 256-bit encryption, solid leak protection, a kill switch, a no-logs policy, and split tunneling to safeguard your online privacy and safety.
Always remember that the dark web is a people-centric community. By the way, most have shipping services. Believe it or not, the dark web even has online shops. You should stay away from everything labeled “porn”, “card skimming services”, “PayPal hacks”, “firearms”, “real fake IDs and passports”.
- You wouldn’t want your email history available on the surface web and searchable by anyone.
- For example, the URL of Silk Road is rather unintelligible and may look something like “gan4arvj452janndj4a76.onion”.
- The experience is reminiscent of searching the web in the late 1990s.
- Whatever your reasons for entering the dark web are, you must follow some crucial steps to ensure your safety so that you can access it in an entirely safe and anonymous way.
- This step-by-step guide is designed to help beginners navigate this hidden part of the internet safely and securely.
Should You Use A VPN And Tor?
It has billions of sites and addresses, it is amazing that we can both search for – and find – anything. Charging the operators with a long grocery list of crimes ranging stolen data, drugs, and malware. The Tor browser is notorious for providing a secure browsing experience and allowing access to the d… Waqas is a cybersecurity journalist and writer who has a knack for writing technology and online privacy-focused articles. However, a slight action or a wrong click on some websites can land you in deep trouble.
User-Friendly

Journalists, activists, and individuals concerned about online privacy and security often use it. Many countries, such as Qatar, China, Cuba, Russia, and Turkey, censor internet content promoting political dissent. People who live under a government that deeply supervises or censors internet traffic eventually get attracted to the dark web. However, it’s illegal if you venture into the dark web to commit unlawful actions such as downloading child porn, buying fake documents, drugs, credit cards, and more. The dark web’s anonymity makes it difficult for law enforcement to track down these criminal activities, leading to a rise in their prevalence. For Example, In May 2021, authorities in Germany brought down Boystown, a child pornography network with more than 400,000 registered users.
Download The Tor Browser
The Tor browser uses the Tor network technology, which encapsulates your data into layers of encryption and hides your IP address. However, Tor remains popular primarily because it is reliable and secure and lets users access the depths of the dark web. These anonymous browsers provide safe and secure access to users on the dark web.
“On the deep web, you can assume that activities are monitored at the gateway. Mail providers Mailbox.org and Protonmail can also be accessed via an .onion link. Any internet traffic leaving the exit node is no longer part of Tor's dark web. With your device running a Tor browser, you can go to Tor-specific sites – those with an .onion suffix — or also visit the usual sites on the open web.
Commercial Services
You should only ever access websites you know are safe because they're vetted by websites or other sources that you already know are safe. But be warned, it's not as user-friendly as the typical clearnet websites you access. It uses the onion router to bounce your signal around other Tor users around the world, thereby pseudo-anonymizing you when you access the dark web. There are many legitimate websites on the dark web that can be worth visiting, but there are also the absolute extremes of illegal material, such as pornography, illegal substances, and gore. It’s also best to only use trusted directories or search engines that show safe links, like Not Evil, to reduce your risk of ending up on fake, malicious sites. Some governments actively monitor dark web activity through various methods, like analyzing internet traffic patterns or using high-end surveillance software.
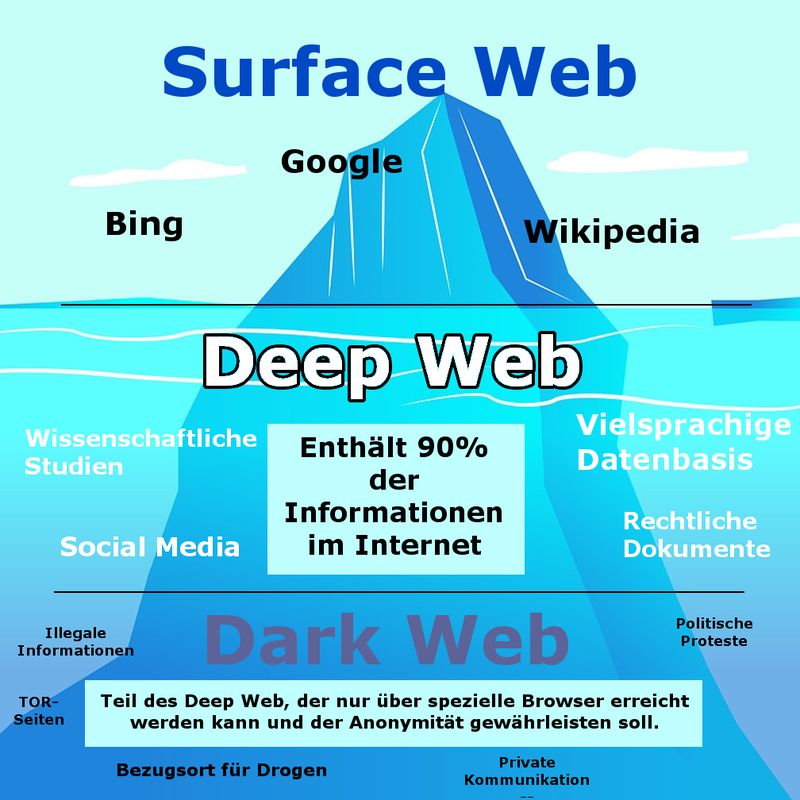
You can also find email messages, online bank statements, and much more information on the deep web – information that is usually private and inaccessible by the public on the surface web. The deep web is basically all the content that you can’t find using Google or Yahoo search. In addition, the content on the pages don’t need any special or custom configuration to access. Pixel Privacy believes in digital privacy and does not believe in using it for heinous and/or illegal activities, and so the focus of this article will be on legal activities.

Secure Your System And Mental Well-being
In this blog, we’ll take a closer look at how these hidden markets operate and the implications they have for cybersecurity and law enforcement. As cyber threat intelligence professionals monitor these markets, they gain insights into emerging threats and malicious activities that can impact organizations and individuals. The darknet is a mysterious and often misunderstood part of the internet, attracting both intrigue and concern. In short, even with Tor, there's no perfect anonymity online, but there are efforts to claw back our power online, says Lewis.
In fact, there are growing concerns about law enforcement monitoring what is happening on the dark web. Government authorities across the globe are taking over many Tor-based sites. Some services are genuine; you can get what you want at an agreed fee. Many services that are allegedly offered on the dark web are scams.

That said, there are reasons some people use the dark web legitimately. As a result, there are plenty of reasons why the average person might choose never to access the dark web. Those marketplaces – and the stories surrounding them – can make the dark web seem like a hive of criminality. Most people have heard of the dark web and the illicit marketplaces available on it. Stay informed about the latest darknet marketplaces, secure browsing practices, and privacy tools.
Search Engines
If you see inaccuracies in our content, please report the mistake via this form. Our goal is to deliver the most accurate information and the most knowledgeable advice possible in order to help you make smarter buying decisions on tech gear and a wide array of products and services. ZDNET's recommendations are based on many hours of testing, research, and comparison shopping. Gannicus Oliver is an experienced tech journalist (he loves writing on emerging techs and digital privacy issues) and an online business consultant. Discovering that your personal data is circulating on the dark web is akin to a personal violation. If you’ve ever worked from a coffee shop and accessed your company’s server, or if two b…



