When it comes to accessing the dark web (and safely), selecting a good dark web browser is critical. But simply using Tor leaves a traceable trail for your ISP; they can see that you’re using Tor. You only need the Tor browser to access the dark web. The correct top dark web browser download isn’t enough when it comes to safely accessing the dark web. Accessing your preferred part of the internet using a specific browser is straightforward. It also comes with several secure pre-installed software programs, including the Tor Browser.
Which Is The Best Free VPN For Tor?
If your incoming traffic passes through a node run by cybercriminals, they could inject malware into the response code. Though most volunteers mean well, others are malicious actors and surveillance agencies. You can never be sure of the motive of the person operating the node that your traffic is routed through. Regardless of what brings you to the dark web, you should be aware of the dangers emanating from the limitations of the Tor network.
It conceals your location and other personal data that are exposed when using standard browsers. The Tor browser routes your online requests through multiple nodes to obscure them from prying eyes. The Tor Browser is a specific web browser, based on Firefox, that utilizes the Tor protocol to enable private browsing. This protocol, a layer built atop the traditional internet layer, routes communication between random servers (called nodes or relays) to obscure the source. It's an overlay network that enables encrypted, anonymous connections between computers. Don’t miss out – collect data without CAPTCHAs or geo-restrictions.
- Tor (“The Onion Routing” project) network browser provides users access to visit websites with the “.
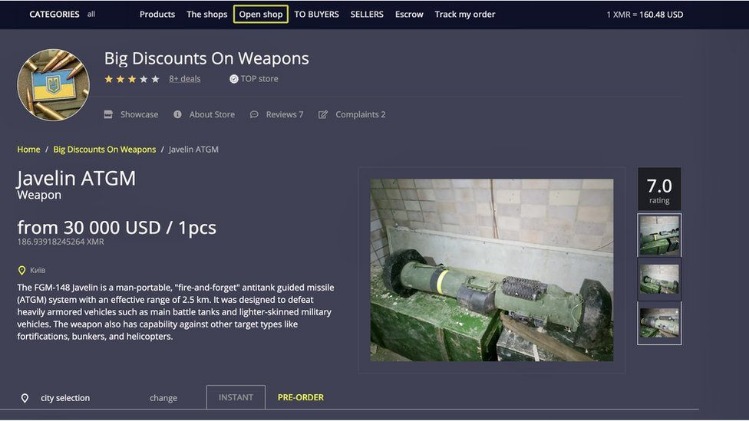
- Because of this, some people use it to get around government restrictions, while others use it for illegal activities like smuggling drugs and weapons.
- Only access the dark web with both a VPN and the Tor Browser active.
- The dark web doesn’t carry as many of the social contracts that website providers follow to protect users on the rest of the web.
- Finally, it is always a good practice to keep your operating system, Tor Browser, and any antivirus or anti-malware software up to date with the latest security patches.
It is important to consider the potential harm and consequences of engaging with such activities. It is important to exercise caution and skepticism when browsing the Dark Web. It is important to be cautious of scams and malware, and to protect personal information while interacting with online communities.
Why Use Tor?
- The browser isolates each website you visit, so it prevents trackers and ads from following you online.
- This requires your connection to go through multiple nodes and relays, which will slow down browsing on Tor.
- The Deep Web isn’t some mysterious underworld—it’s actually a huge part of the internet that you use every day without even know…
- Journalists, activists, and individuals concerned about online privacy and security often use it.
- All connections are encrypted, including public and private keys, and traffic is 'routed', like in the Tor browser, to avoid tracking.
- Yes, the dark web has a dark side, too — such as drugs, stolen data, and all sorts of illegal markets — but that does not mean that it’s just a home for criminals.
Its goal is to offer anonymous access to the content without being censored, no matter where you live. The BBC news website has a special .onion site, which you need to access via the dark web. Facebook’s dark web version allows users to access the site where it is banned or restricted. It does not share IP addresses or web search history to protect your privacy.
Your Data Can End Up Landing Anywhere
In that case, there is a high chance that your data will become accessible to cybercriminals. You should never trust websites and forums on the dark web with your personal information. This prevents anyone—including your ISP—from knowing that you’re using the Tor network.

We also prefer this method because of VPN’s all-encompassing security. Plus, the ISP won’t see that you’re using Tor. When you go on the dark web and visit the site, your traffic is decrypted, and everything functions the same. You get one encryption layer from a VPN, and when you’re in Tor, you get another layer. Some countries frown upon dark web usage, so it’s good to cover your back with a reputable VPN service. A VPN is a confusing factor for many because there are two ways to use it with Tor.
These sites are only accessible over the Tor network and are commonly used for privacy and anonymity. Law enforcement agencies, intelligence communities, and cybersecurity professionals often maintain a presence on the dark web to monitor, investigate, and potentially apprehend individuals involved in illegal activities. The anonymity afforded by the Tor network makes it easier for scammers to operate without fear of identification or prosecution, making it difficult for users to discern legitimate services from malicious ones.
Naval Research Laboratory to protect sensitive government communications. Also, it contains several illegal goods, stolen data, credit cards, and more. It was known for facilitating the sale of illegal drugs, goods, and services using Bitcoin cryptocurrency. Deep down, the tip of the iceberg is where over 90% of the internet content is.
Best Practices For Accessing The Dark Web
The system is designed to provide enhanced security and privacy features. Furthermore, it’s critical to understand that Whonix is not a stand-alone browser. While accessing the dark web using Mozilla Firefox is possible, you must first adjust its settings.

The biggest and most frustrating part about dark websites is that they live for a short span of time. Keybase is a fantastic onion website that lets you cryptographically bring your different online identities together. Right now, you can use many cryptocurrency .onion sites to buy or sell all types of cryptocurrencies.
Step 3: Connect To The Tor Network
On the surface web, if you want to find something, you can simply use a search engine to look for it. If it shows you your real IP address, your VPN is failing in some way, and you should not attempt to access the dark web. This is one last important security check to perform. This is a free, open-source browser that directs your traffic through an assortment of worldwide servers operated by volunteers. Although there are free VPNs, you really need a good paid VPN to access the dark web.
Is It Legal To Access The Dark Web?
If you stick to using it for legitimate and legal purposes and proceed with caution, you can have a perfectly safe and secure experience. However, it’s important to remember there are tonnes of legitimate reasons to use Tor to explore the dark web too. Learn the difference between using Tor and a VPN for anonymous browsing. Don’t get Tor confused with a VPN though, which uses tunnels to protect your data from lurkers. This type of multi-layer encryption means each node, or server in the chain, knows which server your data came from and which server to send it to next.

It is a network of websites and online services that are intentionally hidden and can only be accessed through specific software or configurations. While Tor focuses on broader Internet anonymity, I2P is designed for secure, anonymous communication within its own network, including accessing specific dark web content hosted on I2P "eepsites." This makes Tor a go-to tool for accessing ".onion websites" and performing "anonymous security research". Hidden services refer to websites that are not indexed by traditional search engines and can only be accessed through specific protocols or networks. The dark web is a small part of the deep web that’s only accessible through specialized tools.2 It’s home to websites that run on hidden servers called onion services, and they’re not accessible through normal browsers. Tor’s anonymity has spurred many malicious actors to host dangerous sites on the network, including scams, phishing links, malware, and illegal content.
Discovering that your personal data is circulating on the dark web is akin to a personal violation. If you’ve ever worked from a coffee shop and accessed your company’s server, or if two b… Hence, protecting your online privacy goes far beyo… Your personal data is worth more than you think. Always ensure you get your Tor browser or any other software directly from verified sources only, not from third-party sites. Not just Tor alone, there are official sites for downloading every similar web browser APK.
The deep web encompasses all parts of the internet not indexed by search engines. The dark web forms a small part of the larger deep web, which includes all parts of the internet not indexed by search engines. The dark web is rife with hidden links and malicious content, and a simple misclick can lead to legal trouble if you are not careful.
With long-term plans starting at just over $3/month, it’s also one of the most affordable ways to get premium-level privacy while browsing the dark web. That said, if you’re serious about staying secure and anonymous long-term, NordVPN is clearly the best VPN for accessing the dark web. Speeds were solid for browsing text-heavy dark websites and small links.
Later released as open-source, it became widely accessible for privacy-focused use. Tor, short for The Onion Router, is a privacy-focused network that allows you to browse the Internet anonymously. To access the Freenet-based dark web, you need to install the Freenet application. Freenet is a decentralized, peer-to-peer platform designed for the secure and anonymous sharing of information over the Internet.