While the Tor Browser and the Onion Network are an excellent way to protect your online privacy and anonymity, it is by no means a perfect solution, and it has a few weaknesses. In an onion network, messages are encased in layers of encryption, much like the layers of an onion. All Tor Browser data is encrypted and relayed three times over the Onion Router network, which is composed of thousands of volunteer-run servers, which are known as Tor relays. The Tor Browser automatically routes its traffic through the anonymous Tor network.
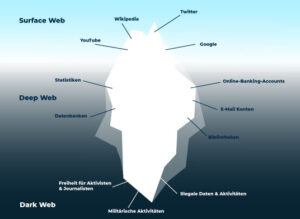
The dark web is web content that exists on darknets, which are overlay networks on the internet that require specialized software (such as the Tor Browser), configurations, and authorization to access. A secure VPN server slows down your browsing much less than the Tor Browser and also opens access to geo-blocked local content around the globe. This encryption and relaying of your browsing data prevents anyone who is watching from detecting which websites you are visiting. You can access these websites without worrying about someone snooping on a Tor exit node, offering more private browsing of what is known as the deep web.
The app leverages the Tor network to prioritize privacy, making it an effective tool for individuals who value confidential web use. Justice has acquired extensive content writing experience over the years. Justice Ekaeze is a freelance tech writer with experience working for specialized content agencies.
Best Free Reminder App With Alarm For Android And IPhone
The Whonix Gateway VM handles Tor processes, and the Whonix Workstation VM runs user applications on an isolated network. If you feel a browser just won’t cut it and want to keep your dark web browsing activity as private as possible, Whonix might be for you. Remember that activity within apps you’re logged into will be recorded, even if you’re using Tor. Orbot is free, open source, and can even replace your VPN, if you don't mind slower browsing speeds. It is worth noting that Private window with Tor isn’t as secure as using the Tor Browser itself. To access the dark net and Tor using Brave, open the browser, choose the hamburger icon from the top toolbar, and select Private window with Tor.
Awazon Market Link And Access Guide 2025
- Epic is created with the Chromium source code, but all Google-specific tracking data code has been removed from it.
- But, how can you get access to all these websites, pages, and information on the deep web and dark web if they can’t be found through Google, Bing, or Yahoo?
- Content includes non-indexed websites, apps, and resources, which can include protected information such as, online banking, specialized databases, non-linked and password-protected websites, and more.
- Whenever you visit any website, click the circuit button next to the domain to open a menu displaying the servers through which your traffic passes.
- Subgraph OS is more than a browser; it is an entire operating system focused on security.
- Although the dark web is rumored to be hard to access, the Tor Browser is just a quick install away.
Just remember, this only hides your browser-based activities and doesn’t hide any of your other online activities. If top-notch privacy is your goal, yes, you can use the Tor Browser for all of your browsing. These can all also make use of Tor’s anonymity features. Other options are the Freenet and I2P (Invisible Internet Project) peer-to-peer networks, both of which provide censorship-free communications.
Data Not Collected
The sandboxing helps isolate your browsing experience extracting the instances where it detects a malware, and then it separates from the standard browsing container. For ensuring anonymity and privacy, it pressurizes all incoming and outgoing connections via the Tor filters. It is a security-oriented live OS and is based on the Debian GNU or Linux. It mentions that the sole reason for enforcing copyrights is generally to entail the communication monitoring that compromises the freedom of speech.

Onion Browser: Tor Dark Web
The surface web is accessible easily as the search engines indexes it. At the first place, the dark web websites and servers are connected by the Tor Network. In this case, the sites are identified with a public key and not with an IP address. It can also be used for publishing websites and sharing files.
What Is WPA2 (Wireless Protected Access ?
You need special browsers, also known as Deep Web browsers, to access the second and third layers of the internet. Always verify the source of onion links to ensure you’re not entering dangerous territory. IOS users can use the Onion Browser, a secure alternative in the App Store. It routes your internet traffic through multiple servers, maintaining your anonymity. The dark web is a segment of the deep web, inaccessible through standard search engines or browsers like Chrome or Safari. While connecting to sites can take some time, slower internet speed is a trade-off for extra security.
How To Install The Tor On Android
It also offers educational insights into network configuration and safe usage practices for browsing the Tor network. The app emphasizes anonymity, making it a suitable choice for individuals seeking to avoid online tracking or intrusive advertisements. He’s handled several projects in diverse niches but loves the cybersecurity and VPN sectors the most. However, using the Tor browser for illegal acts is possible since the network has increased anonymity. The purpose of using Tor is to stay anonymous, and providing any personal data online could comprise it. While using the internet, don’t share your personal details with anyone, including your name, phone number, address, email, and social app profiles.
Enhancing your phone’s security involves disabling unnecessary permissions, such as location, microphone, and camera access, while using Tor. Avoid using your real name, personal email address, or phone number while browsing. Android users, download the Tor Browser app from the Google Play Store or Tor Project’s official website. A VPN encrypts your internet connection, masking your IP address and preventing third parties from tracking your activities. Unlike the deep web (which includes private databases or password-protected sites), the dark web is anonymous and often used for privacy-centric or illicit purposes.

Privacy is a cornerstone of the dark web, but oversharing personal details can compromise your security. Accessing these links requires caution to avoid malicious or illegal sites. Onion links are unique URLs that operate only within the Tor network. Make sure you install updates regularly to fix vulnerabilities and enhance security. Avoid downloading third-party apps that claim to offer dark web access, as they might be malicious.
Upgrading to Safer or Safest mode improves your security but affects website functionality, so you should be aware of the tradeoffs. By default, Tor uses the Standard security level, but you can upgrade it to Safer or Safest. Users can take further steps to maximize privacy when browsing with Tor.
A common inquiry from Tor users is if they should use a VPN to add an extra layer of protection. It encrypts data during transmission to avoid the risk of being eavesdropped. It's what enables web browsers and servers to share information, including web pages and media files. Tor doesn’t support plugins because they introduce security risks. Tor blocks JavaScript by default, but this addon lets you permit it for trusted sites.