Use trusted directories or PGP-signed mirrors—30% of 2025 links are scams. Convert and track cryptocurrency rates for darknet trading. Secure comms with GPG or Kleopatra for vendor deals. Download Tor Browser from torproject.org—your entry to the onion network. Latest shifts in the darknet trading landscape as of February 2025. The top performers of 2025, ranked by trade volume and market influence.
Common Scams On Dark Web Marketplaces
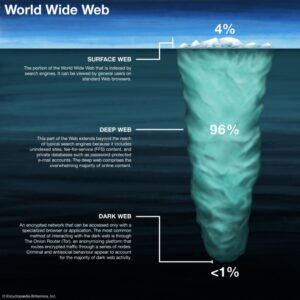
In that sense, the history of the Deep Web is as old as the history of the internet. Despite being much talked about in recent years, darknet stats from a January 2023 survey reveal that 7 out of 10 people in select countries don’t understand what the Dark Web is or how it works. In fact, the Dark Web is a small subset of a much larger Deep Web — a part of the internet containing all the pages hidden from search engines for privacy and security reasons. However, experts estimate it accounts for no more than 5% of the internet. In this overview of recent Dark Web statistics, we’ll start by examining the darknet in the context of the World Wide Web. Links above are generated from existing data and can change as the catalog grows.
Darknet Markets & Onion Mirrors Catalog
The operational security of darknet markets has advanced significantly, moving beyond basic encryption to incorporate sophisticated, user-centric protection systems. Its 13,000+ users and 1,100+ vendors prioritize speed and escrow security in darknet trading. Its 9,000+ users and 700+ vendors focus on drug trades with strong escrow security. Below are 2025’s leading darknet markets, ranked by listings, trade volume, and vendor reliability. Unlike traditional darknet markets, which are hosted on centralized servers and managed by a single entity, decentralized marketplaces operate on a peer-to-peer (P2P) network.
We have seen several markets fail, bust, exit scams. Chainalysis also noted that some markets are openly advertising their wares in Russia, with giant 3D billboards (Kraken Market) and QR codes on subway trains (Mega Darknet Market). “Over the years some markets … developed a robust catalog of illicit services like money laundering, fiat offramping, and products that enable cyber-criminal activities like ransomware and malware attacks. Mcp-scan is a security tool from Invariant Labs that can run as a static scanner or as a dynamic … …More about mcp-scan – Real-Time Guardrail Monitoring and Dynamic Proxy for MCP Servers
This system is designed for user convenience, enabling swift and efficient purchases without the delays typical of conventional banking. To reach a market, one must use the Tor Browser, which is specifically configured to resolve these .onion links. Its foundation is built on a redundant infrastructure of onion mirrors, which guarantees that the platform remains accessible even if individual links are compromised or experience downtime.
Dark Web Marketplaces In 2025
A further PIN may be required to perform transactions, better protecting users against login credential compromise. After discovering the location of a market, a user must register on the site, sometimes with a referral link, after which they can browse listings. The majority of the marketplaces are in English, but some have opened in Chinese, Russian, and Ukrainian.
The ecosystem of darknet commerce is fundamentally supported by specialized directories and verification services, which function as critical infrastructure for secure navigation. High-rated vendors have a clear economic incentive to maintain their standing, directly linking their success to customer satisfaction. Its decentralized nature ensures that transactions occur directly between buyer and vendor, eliminating the need for a central authority that could be compromised or serve as a single point of failure. For procurement, the platform supports a streamlined logistics framework, enabling vendors to manage orders and shipping details with a high degree of automation and discretion.
Its 11,000+ users and 850+ vendors value its enduring stability since 2019. With 14,000+ users and 1,000+ vendors, it’s a versatile crypto commerce powerhouse. Its operational model focuses on providing an efficient service, functioning as a darknet drug store with ready access. For practical access, users depend on updated market lists and verified links to locate a functioning gateway. Many platforms function as highly efficient stores, offering ready access and a user-friendly interface that rivals conventional e-commerce. The darknet drug market continues to evolve with improved darknet market links and darknet market lists.

Trade Craft
- When AlphaBay went offline on July 4, many fleeing users migrated to Hansa which was by then run covertly by police.
- Markets that lack proper security often become targets for law enforcement, scammers, or cyberattacks.
- The immutable nature of the blockchain and the predictable behavior of a well-designed market wallet system work in tandem to secure both access and financial transactions.
- With a growing user base and expanding inventory, Vortex is positioning itself as an “all-in-one” darknet marketplace.
- This set the legal precedent that even Tor hidden markets are prosecutable.
- Vendors like “ViceRx” and “PillMaster” offer 97% reliability, though stock shortages (5–10%) limit variety outside drugs.
Here, you can find anything from stolen credit card information and personal data to illicit drugs and counterfeit goods. One of the many creepy Dark Web facts is that marketplaces don’t just sell forged and stolen documents and credentials — they also sell malicious software hackers can use to infect their targets. Worse yet, it was the largest marketplace for illegal drugs in all the countries of the former USSR. Back in 2020, this Russian-speaking marketplace was the world’s biggest darknet market.
Dark Web Statistics By Largest Marketplaces
Modern platforms have integrated more sophisticated wallet systems that streamline the deposit and withdrawal process, minimizing user error and the potential for lost funds. Its decentralized nature provides a layer of financial anonymity, allowing users to engage in trade without direct ties to their real-world identity. Reputable markets now maintain multiple, verified mirror links that are easily found through dedicated, clearnet indexers and forums. This multi-layered encryption ensures that personal data and financial activities remain confidential, effectively separating a user's identity from their actions on the network. To use social login you have to agree with the storage and handling of your data by this website.
Incognito Market Vendors
The interface is designed for intuitive navigation, allowing users to browse extensive product categories, compare vendor ratings, and complete transactions with minimal effort. Look for vendors with a solid reputation and a history of positive transactions. Can I trust vendors on these markets? Commentators have suggested “multi-sig” crypto payments — requiring multiple keys to authorize a payment — and OpenBazaar, a fully-decentralized marketplace for e-commerce transactions. In recent years, some marketplaces have expanded onto platforms like Telegram to broaden their reach and cater to cybercriminals seeking to expand or develop their dark web activities.
Hacked credit cards are the bread and butter of the dark web economy in stolen data and prices remain stable at around £33 per account. We are also currently seeing more hacked bank accounts for sale that have high balances, giving criminals access to thousands of pounds instantly. For the purposes of the Price Index, we disregarded dumps as unit prices work out at tiny fractions of a cent each and the accounts in these dumps are not guaranteed to be accessible or even valid. The majority of the hacked accounts we found in this category were being sold by a single seller on Dream Market, the dark web’s biggest market.
Once a legitimate link is acquired, users navigate to a user-friendly shop interface designed for streamlined and efficient trade. Markets that maintain consistent uptime and reliable access through a robust system of mirrors ensure that transactions can be completed without unnecessary delays. For the user, this translates to predictable access and the ability to conduct business without interruption. A market with a long-standing reputation, such as Nexus, will have its mirrors widely distributed, making it a consistently accessible option.
Only 67% Of Tor’s Daily Users Engage In Illegal Activity On The Dark Web
These sites cater to cybercriminals seeking valuable data, such as credit card numbers, login credentials, and personal information. As of 2020, nearly 57% of the dark web was estimated to contain illegal content, including violence and extremist platforms. Today’s cybercriminals spread their activities across multiple platforms, making them harder to track and shut down. Dark Web Marketplaces continue to thrive as central hubs for these illicit transactions.

The practice of using mirrors is a fundamental aspect of operational security, providing redundancy and ensuring that a marketplace's services remain available. Relying on these community-vetted sources is a practical method for bypassing access barriers and maintaining a direct line to the marketplace. These platforms provide user-reported status updates and newly verified URLs, creating a collective intelligence system for access point reliability. These repositories are regularly updated to counteract any service disruptions, ensuring that users can reconnect with minimal downtime.
It was the first big site where people could anonymously buy drugs using Bitcoin, and it gained a lot of attention, until it was shut down by the FBI in 2013. By supplying stolen data, these dark web links fuel many online scams and identity theft operations, playing a critical role in the darker aspects of the internet. Ransomware and cryptocurrency-based crimes saw a significant increase in 2025, with $2.17 billion stolen from crypto platforms, surpassing the total for all of 2024. Freshtools was established in 2019 and offers various stolen credentials, accounts, and host protocols like RDP.