As a result, the trading of illegal goods online has become more commonplace, and vast dark web marketplaces have been created. Deep web marketplaces are online marketplaces where people can buy and sell illicit goods and services under the protection of the anonymity of the dark web. No, it is not illegal to access the Dark Web or use Tor.However, accessing illegal content (e.g., child exploitation material, drug markets) is a crime. A top-of-the-line VPN network that ensures maximum security while accessing dark sites online. For example, the Silk Road site operator, an illegal dark web marketplace, was traced and arrested.
How Darknet Markets Run Smoothly
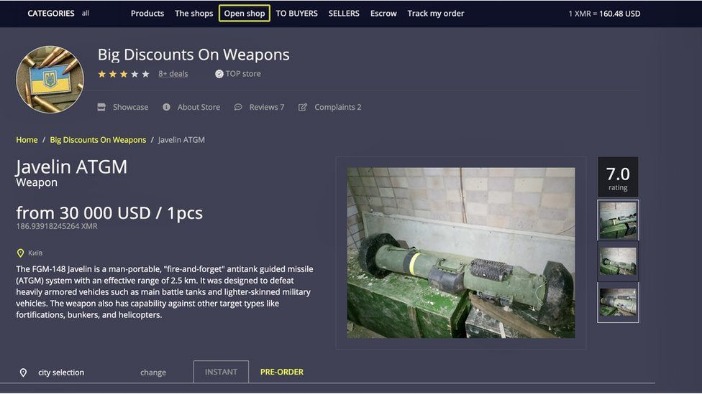
Specialized search engines, directories, and wikis can help users locate the data they’re looking for. It has gained a lot of users and has become a popular marketplace due to its focus on security. A network browser gives you access to sites with the ‘.onion’ registry operator. Its interface resembles legitimate marketplaces, making it accessible to technically proficient threat actors. In this article, we’ll explore the top 10 dark web marketplaces, how they operate, and what businesses can do to monitor and protect their data from exposure.
About Black Market & Darknet Markets
It is a wallet-based shop, meaning you must first deposit bitcoins into your wallet before purchasing any goods and services. DarkFox Market is the largest dark web shop selling various products and attracting more vendors and users. It blends illegal trade with features like gambling, all while maintaining a clear and accessible structure. Vortex aims to stand out by being user-friendly, secure, and anonymous. During our tests for the research, we were able to register with a bogus email and a random username. It offers a wide range of goods and services with robust anti-DDoS protection (with military-grade security protocols) and no JavaScript, ensuring privacy and uptime.
How To Get The Tor Browser
The user interface on these platforms rivals that of mainstream e-commerce sites, featuring intuitive search functions, vendor rating systems, and detailed product listings. The landscape of darknet commerce in 2025 is defined by a selection of highly specialized platforms that prioritize transactional security and user experience. Nexus market url and other darknet market links offer a streamlined experience for acquiring goods from a darknet drug store. For additional security, users are advised to tumble or mix their coins through a trusted service before depositing funds into a market wallet, breaking the link between their clean coins and the market deposit address. These lists function as a vetting mechanism, distinguishing platforms with a proven history of operational security and reliable vendor transactions from newer, less stable alternatives.

Its look, design, options, and interface are exactly the exact copy of its competitor, but everything else, including buyers, vendors, and servers, is different. Besides this, it supports wallet-less transactions and accepts payments through Bitcoin, Litecoin, Monero, and Zcash. However, the platform lacks an advanced search option and a wallet-free payment option. It was quite popular for selling a wide range of products and services.
Safer And More Private Darknet Purchases

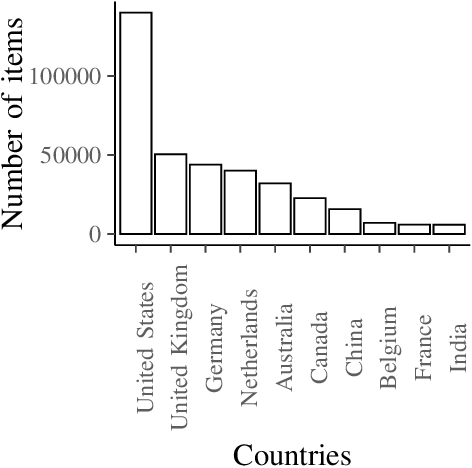
One such study was performed on Evolution, one of the most popular crypto-markets active from January 2013 to March 2015. Examination of price differences in dark web markets versus prices in real life or over the World Wide Web have been attempted as well as studies in the quality of goods received over the dark web. These markets have attracted significant media coverage, starting with the popularity of Silk Road and its subsequent seizure by legal authorities. As of December 2020, the number of active Tor sites in .onion was estimated at 76,300 (containing a lot of copies). Tor browsers create encrypted entry points and pathways for the user, allowing their dark web searches and actions to be anonymous.
A VPN hides your internet activity, making it harder for your connection requests to be traced back to you. Think of it as the internet’s wild card. But even though it seems like there’s a lot out there, this only makes up about 4% of the entire internet. This is where all the cat videos and trending YouTube songs live, easy to find and access. When you search for something on Google or Bing, you’re using the clear web. The Dark Web is a hidden part of the internet, completely different from the clear web we all use daily.
Secure Your System And Mental Well-being
Abacus Market quickly rose to prominence by attracting former AlphaBay users and providing a comprehensive platform for a wide range of illicit activities. Threat actors use these platforms to buy or sell assets originating from corporate environments. Marketplaces intentionally limit accessibility to maintain operational security. These hidden platforms act as trading hubs for stolen data, leaked credentials, malware tools, and other illicit assets that directly threaten businesses of all sizes. Educational analysis of black market online store economics, cryptocurrency usage, and the underground economy ecosystem.
Darknet Markets & Onion Mirrors Catalog
“If so, I think that Telegram is no longer a realistic platform for these marketplaces, and they'll have to look for somewhere else to operate.” He suggests the crypto-scam market operators would then likely try to migrate to another messaging service with less oversight, or even a decentralized one where they can't be effectively banned. Elliptic's latest findings concerned a second Telegram-based market known as Xinbi Guarantee, which offered a similar model of third-party transactions and had facilitated $8.4 billion in deals since 2022 that researchers say included not only money laundering for scammers, but also stolen data, harassment for hire, and apparent sex trafficking. By Elliptic's accounting in a January report, the market and its rebrand had facilitated more than $24 billion in total transactions, which would make it by far the largest single black market operation in the internet's history. The move comes in response to Telegram's action on Monday to ban thousands of accounts and usernames that served as the infrastructure for the sprawling marketplace of third-party vendors, many of whom provided money laundering and other services to the burgeoning industry of East Asian crypto scammers. Our continuously updated content provides in-depth insights into marketplaces, ransomware actors, and hacking forums, helping you stay informed and proactively address challenges to safeguard your organisation or community.
- Stolen data can quickly transition from legitimate systems to underground forums, where it becomes a valuable commodity for cybercriminals.
- Silk Road, launched in early 2011, was the world’s first major Tor based marketplace.
- This process effectively anonymizes the origin and destination of all data packets, creating a secure tunnel for communication and transactions.
- You can now safely browse dark web websites and hidden wikis, but if you plan to do anything more than that, you’ll need to take several precautions.
- These sites are a hybrid tutorial-underground where wannabe hackers ask questions and professionals sell their services or stolen data.
Within this hidden layer, dark web markets serve as underground bazaars for data, malware, counterfeit goods, and illicit services. These dark web marketplaces operate outside traditional oversight, making them a persistent challenge for cybersecurity teams and law enforcement. Security teams use the dark web to monitor criminal forums, marketplaces, and communication channels for early warning signs of threats. Many marketplaces and services operate without oversight, making fraud rampant. Naval Research Laboratory developed onion routing, a method for encrypting and relaying internet traffic through multiple nodes to conceal its origin. Quality and validity of the data it provides justify its higher cost over other marketplaces.
Agentic AI-Powered, Intelligence-Driven Unified Cybersecurity Platform
The process of acquiring goods is intentionally straightforward, minimizing friction and maximizing efficiency for the user. This combination of a polished interface and multi-layered security measures creates a reliable environment for commerce. Navigation is intuitive, with clearly labeled categories and a streamlined checkout process that mirrors the efficiency of mainstream e-commerce sites. Modern platforms have moved beyond the clunky and intimidating interfaces of the past, adopting design principles that prioritize clarity and ease of use.
- Data, whether in the form of simple user credentials and passwords or proprietary trade secrets, can fetch quite a price on the dark web.
- Such launches were not always a success; in February 2014 Utopia, the highly anticipated market based on Black Market Reloaded, opened only to shut down eight days later following rapid actions by Dutch law enforcement.
- This website allows you to type in your email address or phone number and see if it’s been compromised in any data breaches.
- Nowadays, many people use the Tor browser to surf the public internet and navigate the deeper parts anonymously.
- Machine learning is another big player here—it helps by analyzing data to predict and identify suspicious behavior much faster than a human ever could.
It marketed itself as a black market bazaar and sold everything from marijuana to heroin, plus hacking tools and counterfeit IDs. The dark web is not as dark as you think, warns Europol law enforcement uses specialized techniques to unmask hidden transactions. KEY TAKEAWAYS Whether you are using Android or iPhone, you can easily access the dark web on your ph… KEY TAKEAWAYS The Deep and the Dark web are the hidden part of the internet. KEY TAKEAWAYS If you live in a country where you don’t have internet freedom and face extreme … It uses the Tor network because it is a popular network that helps to circumvent censorship and online surveillance.
What Is The Dark Web? How To Use Tor To Access The Dark Web
The dark web refers to content on the internet that is intentionally hidden and requires special software like Tor Browser to access. Then, use data breach monitoring software to help find out if your personal data has leaked onto the dark web. The websites you visit every day aren't all there is to see on the internet — not even close. There's no such thing as perfectly private or secure on the internet. "All of your traffic goes through it, and you have to trust them as if they are your new ISP. Because the backbone of our software is a decentralised network, you don’t have to trust us to browse the internet privately." To review security settings, click on the onion logo in the top left and select "Security Settings", which will bring up a slider offering a choice of the default of standard, or safer and safest.