Given how security conscious DeSnake was previously, which they self-proclaimed as operating under the mindset of ‘the agencies are after me’,” it is unlikely that they would have been comfortable writing in such recognizable patterns and thereby potentially exposing speech and language nuances. While DarkOwl generally avoids engaging in or commenting on speculative darknet drama, there are several things about the re-emergence of AlphaBay and DeSnake that don’t add up. Some users claim that mr_white and his team from WHM are to blame for last week’s DDoS while others speculate that HugBunter himself could be mr_white. During this research, DarkOwl discovered a surface web domain that mirrors much of the information DeSnake shared on Dread, but with a Tor link to the market that is not in the mirrors.txt verified links list from AlphaBay. Unfortunately, DeSnake’s contributions written in a mixture of English and Russian backfired and senior members of XSS berated them for their lack of operational security and inability to properly understand the dynamics of the Russian language. AlphaBay historically had a vocal and persistence presence on Darknet Market Avengers forum which unfortunately, has been offline for several weeks.
Escrow Systems:
Hence we do not distinguish multisellers by the number of markets in which they operate. We assess the strength of a market’s dominance by the market share (i.e., the market revenue divided by the sum of the revenues of all markets) and by the length of the time interval the market remains dominant, as shown in Fig. Moreover, we find a change of trend between the seller and the buyer median net income time series which reflects the dominance of markets, as detailed in the next section. We consider the whole ecosystem, i.e., all markets and the U2U network. Therefore, an entity can be classified as a seller in one or more markets and/or the U2U network simultaneously.
Largest Dark Web Marketplaces By Share
Moreover, the number of multibuyers increases, which suggests a fast response from buyers to external shocks by trying to diversify their sources. On the other hand, the number of U2U-only buyers is less affected. The U2U-only category is comparatively small, representing only 6% of all buyers on average. The results for buyers are different, as shown in Fig. Interestingly, while the other categories of sellers show signs of recovery relative to their previous levels, the number of multisellers remains low after that shock (see Supplementary Information Section S4).
Darknet Threat Monitoring With KELA
By leveraging automated dark web monitoring, organizations can mitigate risks, and take preventive measures before the leaked data is exploited. Manual monitoring of the dark web is inefficient and risky due to the sheer volume of data involved. BidenCash, established in 2022, is notorious for its involvement in selling stolen credit card information and personally identifiable information (PII). FreshTools, founded in 2019, specializes in selling stolen account credentials and data, particularly webmail, RDPs (Remote Desktop Protocols), and cPanels. Their specialty is selling stolen data, including login credentials, credit card information, and compromised accounts.
This feature is satisfied when \(\phi _i(t) \le \tau\), where \(\tau\) is the maximum value of mean interevent time. This feature is satisfied when \(\ell _i(t) \ge L\), where L is the fixed value of minimum lifetime. Fifth, we consider the lifetime of each entity i at time t, defined as the time interval between the first and the last transaction performed by the entity until time t, denoted by \(\ell _i(t)\). For each entity, we keep track of the cumulative values of the six features for each transaction performed by the entity over time. While the Bitcoin blockchain is publicly available on Bitcoin core37 or other third-party APIs such as Blockchain.com38, a market or a user can generate a new address for each transaction. Additionally, transactions are made with cryptocurrencies, mostly Bitcoin, which also provide anonymity to the transaction parties6,36.
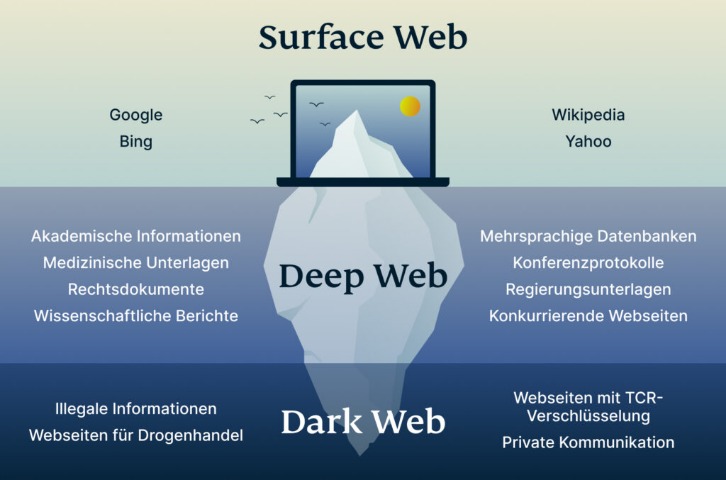
Since the dark web can be accessed through the Tor browser, use a VPN with the Tor browser to ensure increased protection. We recommend using NordVPN as it offers top-notch security features, including dark web threat protection. It also masks your IP address, making it difficult for government agencies to monitor or track your activities. A VPN encrypts the data traffic and keeps your activities private on the dark web. It allows access to the .onion sites on the dark web that you won’t find using a regular browser. users comments were generally critical of the legitimacy of the marketplace, with comical references like “Welcome to the FBI HQ” posts. Dread staff “vouched” for DeSnake to skeptical darknet users with DeSnake signing documents using their historical PGP key.|Despite being much talked about in recent years, darknet stats from a January 2023 survey reveal that 7 out of 10 people in select countries don’t understand what the Dark Web is or how it works. This includes everything from academic papers and government documents to private, password-protected data like online banking, medical records, and email accounts. According to estimates, the size of this hidden web stands at 7,500 terabytes — making it about 400 times larger than the Surface Web. However, experts estimate it accounts for no more than 5% of the internet.}
- Awazon Market is a top-tier dark web marketplace with claims to revolutionize secure anonymous commerce.
- One China-based pill press manufacturer which advertises on clearnet business-to-business (B2B) websites has on-chain ties to drug vendors on Abacus Market.
- As dark web threats grow more sophisticated in 2025–26, regulatory frameworks and legal boundaries are evolving to govern how organizations and law enforcement respond.
- The intermediate resilience regime of the S2S network.
- The ASAP is a moderate design marketplace on the dark web that offers helpful tools like mandatory PGP encryption and two-factor authentication for a safe browsing experience.
- And, perhaps the most aggressive marketing stunt the darknet market ecosystem has seen yet, in December of that year, Kraken Market wrapped a bus in an advertisement that included a QR code for the market’s website.
Law enforcement agencies monitor many dangerous markets, and even anonymous browsing isn't foolproof. Even if you've never visited these markets, your personal and financial data might already be there, having been leaked through a data breach. Most buyers and sellers use the Tor network, which hides IP addresses and locations. By relying on encryption, pseudo-anonymous currencies, and network-level anonymity, they create a false sense of safety, drawing in both buyers and sellers. Most dark web marketplaces mimic familiar e-commerce websites. A dark web market is a hidden online platform where users can anonymously buy, sell, and trade illegal or sensitive items.

Some markets are invite-only or have strict registration rules to keep out scammers and law enforcement. Believe it or not, some dark web marketplaces have pretty advanced systems for building trust. Others are looking for stolen data, hacking services, or even banned books and political content.
China-based Vendors And Novel Synthetic Opioids

Currently there are 12 actives listings, and the below screenshot shows 3 financial counterfeit products. The counterfeiting category on Dark Empire Market primarily advertises counterfeit financial products. Counterfeit goods are products that are made to imitate genuine items with the intention of deceiving others. They provide an email that can be used for any enquiries or issues – offering full customer support to the users on the site.
- The data provides insight into the scope and operations of forums, marketplaces, and extortion groups that reside on hidden services.
- For example, to obtain a monthly time series of sellers, we compute the union of the lists of sellers for each month.
- Chainalysis data shows darknet marketplace revenue dropped post-Hydra seizure in 2022 but recovered to $2 billion in Bitcoin inflows during 2024 Darknet market BTC inflow drop and shift to Monero.
- Founded by Ross William Ulbricht in 2011, Silk Road quickly established itself as the go-to destination for illegal items, particularly illegal drugs.
- This further complicates monitoring efforts because now you need to search for the related Telegram channels and track activity there and on the marketplace itself.
- Financial fraud is common, and you have no recourse if transactions go wrong since these markets operate outside legal frameworks.
Emerging Threats On The Dark Web (2025–
Due to its extensive inventory and reputation for reliability, Brian’s Club has maintained a significant presence on the dark web. Accessing them may require .onion links and the Tor browser, but caution is advised due to legality and cybersecurity risks. Cybersecurity experts should pay close attention to these trends, as they often indicate emerging threats and profit-generating tactics among the cybercriminal forums. Active for a decade since 2014, it is a widely used credit card shop used to source stolen credit card information such as dumps, CVVs, Wholesale Accounts.
Hydra Market 2015 2022 Europe’s Drug Giant
However, after the operation Bayonet, although the network shows a decrease in connectivity, it still remains highly connected and with a large number of active multibuyers. The width of the edges is proportional to the number of multihomers acting between the markets. The most affected are multisellers, with a drop of 78% in the median income, followed by market-U2U and market-only sellers, with a drop of 59% and 47%, respectively. This suggests that sellers with more diverse sources of income, such as multisellers and market-U2U sellers, are able to produce a higher income. They are followed by market-U2U sellers, then market-only sellers, and lastly U2U-only sellers. However, compared to sellers, the drop is notably smaller, and the number of buyers rapidly recovers to previous values.

Darknet Markets Explained
If the address is in one of the cybercrime datasets, the person will receive an email that includes personalized instructions on how to clean up their computer and make it safe again. Given the tooling’s ability to capture new password updates, the perpetrators could easily maintain control over his accounts, and they opened bank accounts in his name and had his physical mail sent to an address where they could receive it. Any time the information-stealing malware detected changes to a victim’s passwords or a new account, it would update the Genesium browser with the latest credentials. The information-stealing malware package that Genesis Market used to exploit victims included a hidden Chromium-based browser plugin, made to look like a Google Drive plugin, which captured credentials stored in victims’ browsers. In order to gain control of victims’ computers, the malware Genesis Market employed used a legacy Bitcoin address to determine the command-and-control (C2) server, from which cybercriminals initiated remote access to infected devices. We spoke with Ruben van Well, Chief Inspector of Team Cybercrime Rotterdam from the Dutch National Police, to learn about their involvement in the Genesis Market case, and how the Genesis operation worked.
Darknet Marketplace Analysis
The revenue generated during this period exceeded $140 million, but that figure now seems modest compared to current market volumes. Organizations must implement comprehensive data theft prevention strategies to protect their assets. Hackers serve as producers, breaching systems to obtain raw data.
The vast majority rely on the Deep Web and the Dark Web to provide them with freedom and anonymity while browsing the internet. Although it only constitutes a tiny part of the Deep Web and an even tinier part of the internet, the Dark Web is by no means insignificant. Attacks with a smaller number of requests typically sell for less, and the target networks’ protection level also impacts the price. Ranging from $10 for an hour-long attack to $750 for a month-long attack, each with 10,000–15,000 requests per second, the prices depend on a variety of factors. Not only is the Dark Web’s DDoS market still active in 2023, but the prices of attacks are lower than ever.
Coordinate Intelligence With Incident Response
The darknet and dark web are also occasionally confused with the “intellectual dark web,” a loose collection of neo-reactionary thinkers (and not a specific part of the Internet). The concept of the darknet is closely related to the dark web, but the terms are not entirely interchangeable. Darknets may be small and intended just for groups of friends or much larger, like the popular Tor network. Our editors will review what you’ve submitted and determine whether to revise the article.
You can use a dark web scan tool to tell if your data has landed on the dark web. The unique part is that the platform offers free samples of stolen information, often to attract more customers. It’s the place where you can buy or sell stolen credit card numbers, SSH login credentials, and personally identifiable information (PII).



