While you can visit the obscure part of the internet without a VPN, it’s better to go with one. What about websites that restrict Tor connections? The downside is that some websites block Tor connections by detecting its exit node. This means you can go on the darknet privately while downloading torrents on the side.
Security Links
From the time of its emergence (the mid-1990s), government agencies have experimented with onion routing to protect communications of sensitive information. In the dark web, you can come across forums, markets, and hidden communities. ” from a business perspective, you will learn how anonymity can be used for both good and bad purposes. Exploring the Dark Web environment is critical for companies whose security depends on digital evidence. Install Avast SecureLine VPN for iOS to protect your privacy and keep your data from falling into the wrong hands. Install Avast SecureLine VPN for Android to protect your privacy and keep your data from falling into the wrong hands.
Do I Have To Use A VPN?
ProtonMail’s .onion link provides encrypted email services, ensuring privacy and security for users accessing it via the Tor network. Dark web links are unique .onion URLs that grant access to hidden websites on the dark web, which can only be reached using the Tor browser for privacy and anonymity. On the basis of the many stories that go around related to the dark net and the anonymity of the users, it is easy to get the impression that the network is intrinsically illegal. Websites on the darn net can only be accessed directly with the help of anonymisation networks such as Tor ("The Onion Router") or via dark net search engines. Similarly, people in countries with strict internet access and usage regulations must use Tor clients or virtual private networks (VPNs) to access some public websites. For instance, the search engines won’t be able to access the servers and websites hosting data about some government-led secret alien mission.

The editorial team did not participate in the creation of this guide. If you manage not to expose your private information and avoid illicit activities, you can be sure everything will be okay. Stick to tried-and-tested sites and do your best to avoid scams.
Yes, you definitely need a VPN if you want to access the dark web on your phone. If your information has been compromised, then it’s likely that your phone number is also on the dark web. Just note that although you’ll be anonymous, you won’t have the speed or convenience of a direct connection, and some sites might block you outright. One of the great things about Tor is that it can be used to access both the dark and surface web. Connecting to the Tor network might raise eyebrows depending on who and where you are.
If that happens, you can guess what happens to your data then. During that period, on top of the risk of accidental disclosure and theft, governments and the police could ask ISPs to share data. These laws mark how long ISPs must save the data they collect.
When you use the Tor network, your traffic is layered in encryption and routed via a random relay, where it's wrapped in another layer of encryption. "If you access 'facebookcore' you are definitely connected to Facebook, because of the nature of Onion addressing — no DNS or Certificate Authority censorship mechanisms are applicable." "The Tor network is another network which sits on top of the TCP/IP internet, stitching the participating computers together into a wholly new network 'space', not IPv4, not IPv6, but 'Onion Space'." That may seem an extreme way to browse the web, but such protections are increasingly worth considering, says Sarah Jamie Lewis, executive director of the Open Privacy Research Society.
Moreover, malicious actors can attempt phishing scams to steal your data and identity for extortion. All in all, it is not illegal to access the dark web, but it can create issues for you. For example, perpetrators of trafficking and cyber attacks use the dark web to disguise their actions.
Can A VPN And Tor Make The Dark Web Completely Private And Secure?
The entry node encrypts your traffic, and it bounces across several nodes in the Tor network until it reaches the exit node. So, to clarify again, this tutorial will cover how to access the dark web privately and safely – not the deep web. You need a special browser (Tor), and all these websites are intentionally obscured.
Marketplaces For Everything Illegal
Remember that illegal activities can still incriminate you, whether you are using a Tor browser. People in countries with heavy internet censorship must get a VPN or Tor browser to access the surface web. It is a good way to prevent third parties from tracking online activities.

Many credential-theft operations rely on info-stealer malware campaigns that extract browser-stored passwords and authentication tokens. Law enforcement agencies regularly emphasise the scale and impact of such phishing and impersonation networks. Several 2024–2025 ransomware incidents began with leaked corporate VPN credentials appearing on dark web search platforms. A 2025 assessment of dark web monitoring practices described how businesses increasingly track leaked credentials and impersonation attempts through unified dashboards. Consumer-oriented guides have been replaced by platform reviews focused on API access, automated scanning, and integration into SIEM pipelines. As demand grows, enterprise organisations now treat dark web monitoring as a staple of external threat intelligence.
- These websites will now work without issues, as the VPN hides the exit node and makes your traffic look inconspicuous.
- We highly recommend employing another layer of security via a VPN.
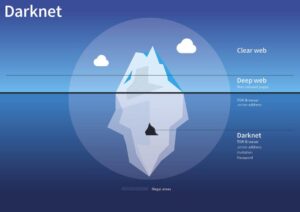
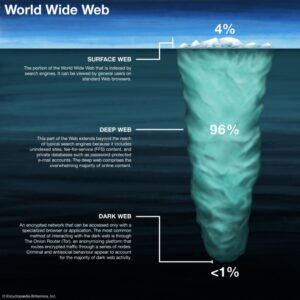
- The Dark Web is said to be 5,000 times bigger than the surface web, and yet, it cannot be accessed through a normal browser or a search engine.
- The darkest corners are used to hire hitmen, engage in human trafficking, and exchange child pornography.
Naval Research Laboratory to enable secure and anonymous communication. It works by routing your encrypted traffic through multiple volunteer-operated servers, known as onion routers. Like Freenet, I2P has its own dark web that consists of websites ending in b32.i2p. It works as a decentralized, peer-to-peer network that emphasizes censorship resistance and complete anonymity.
What Is The Surface Or Open Web?
Ironically, the Tor network surfaced in 2006 from a legal project jointly funded by the U.S. For example, it can help users communicate in environments or geographical areas where free speech isn't protected. Despite its many shadowy uses, the dark web itself is not illegal, and it supports several legitimate uses. Often, dark web visitors use cryptocurrencies such as Bitcoin to engage in such e-commerce transactions anonymously with reduced risk of being caught. This is because these sites have an unconventional naming structure.
Keep Your Data Off The Dark Web
Countries such as China (and its famous "Great Firewall" blocks) may monitor citizens at the Internet Service Provider (ISP) level; if you are using Tor, the usage alone may appear in your records. Unless you know exactly where to go to access a legal and legitimate website, you need to be aware of some of the risks you might be taking. You should remember that in most countries, accessing dark web resources is legal. DefCon, ProPublica, the CIA, various libraries, and open-source software providers also feature in this area of the internet. To access a dark web resource, you will need to know its web address to the letter. It will normally take a while to connect because Tor — unlike other browsers — will route your traffic through different nodes.
Despite the sinister name, the Dark Web is only one part of the overgrown internet that is much larger than what most search engines show. The idea that there are only malicious or technical gurus does not reflect the truth that the onion services draw all sorts of people. From slow network connection speeds right up to the point of being a hunting ground for scammers, this hidden internet is far from being smooth.
How To Use Tor Browser Safely
Exploring the dark web can seem mysterious, but with the right guidance, it becomes a valuable tool for privacy, security, and uncensored access to information. To learn how to safely access the Dark Web sites listed above, read our Dark Web Access Guide here. Dark web links operate on a system of layers (like an onion) where each layer encrypts traffic as it passes through multiple relays. The project is widely regarded as a cornerstone of internet anonymity, supporting activists, journalists, and individuals in restrictive regions worldwide. The .onion version helps users in restrictive regions or those looking for more privacy.
With all this data, your ISP could create a very accurate profile of you and link it to your IP address. It is highly advisable to take all the necessary security measures discussed in this article to protect yourself. You can access the dark web using your Android device by following a few steps.
Rely On Secure Browsers (eg, Tor)
It hosts both legal and illegal activities, offering anonymity but also posing risks like scams and illicit content. And, of course, people, websites and third-party trackers will know who you are if you choose to identify yourself online. If you use the Tor browser to access a standard website, it offers protection and anonymity to users — they pop into the Tor cloud, that "onion space", and pop back out virtually elsewhere, with their identity and location obscured. Tor refers to "the onion router", which is a network that bounces your traffic through random nodes, wrapping it in encryption each time, making it difficult to track; it's managed and accessed via the Tor browser.