Tor is specifically designed to mask your real IP address. Highly resourceful adversaries (like some government agencies) may sometimes have techniques to de-anonymize Tor traffic. However, your anonymity also depends on how you use the browser. By following these guidelines, you can explore the power of privacy while browsing online.

Is Tor Completely Anonymous?
Tricky, but effective; that’s why it’s, by far, the best method to access dark web content. Instead, download Tor, the most secure and user-friendly option for accessing .onion sites. Crimes range from data theft and selling illegal goods for cryptocurrencies to human trafficking and more severe offenses. Instead, sites have complex .onion addresses, making them difficult to find without the exact URL. Privacy and anonymity are the dark web’s hallmarks, thanks to a network of servers that hide users’ identities and locations.
- Finally, Wasabi Wallet is non-custodial, meaning you alone can access the encryption keys.
- It routes internet traffic through a network of volunteer-operated servers, concealing the user’s IP address and encrypting their communications.
- For most users in locations where the Tor network is not censored or restricted, a direct connection is usually sufficient and the simplest option.
- The dark web is designed for anonymity via networks like Tor.
- If you are reading this, you’ve likely heard about how the Tor Browser can help protect your internet privacy and anonymity online.
Is It Illegal To Access The Dark Web?

As hoped, the Tor anonymous network grew in popularity among computer enthusiasts, privacy advocates, journalists, dissidents under repressive governments, and others desirous of strict secrecy. Our editors will review what you’ve submitted and determine whether to revise the article. The Tor Project website provides explanatory introductions, manuals, blog posts, and FAQs about everything Tor. The myth of it being a tool only for nefarious, abject activity counteracts its potential for being known as a tool for access, democracy, and justice. For details on this logic, check out the description of entry guards in Tor’s FAQ. This observer could be able to see the flow in and out of each side, and use timing correlation to identify what traffic you’re creating.
ISPs have been known to throttle internet speeds and even contact customers about Tor usage. Still, Tor and the dark web have a stigma attached due to the undercurrent of illegal activities. If you’re not engaged in illicit activities, it’s not a crime to use the dark web to protect your privacy.
Accessing Onion Sites On Android
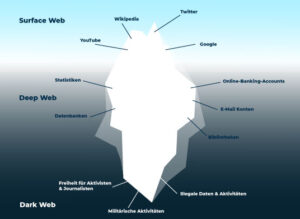
This node decrypts your traffic, and it reaches the destination, i.e,. While the Tor Browser is great and safe, it’s not as great as another component – a VPN. Compare this to getting on the dark web and the way that part of the internet works. Some hospitals even have classified medical records you can’t access just like that. The same goes for private networks belonging to companies and other entities. They have their Gmail inboxes accessible only to them.
Is There A Search Engine For Onion Sites?

My testing showed it loads quickly and offers the same high-quality content as its regular website, making it an excellent resource for readers in censored regions. ProPublica provides Pulitzer Prize-winning uncensored investigative journalism through its .onion service. I especially like how TorLinks categorizes links based on their type, letting you easily find what you need. Its strength lies in regular updates and community-driven verification of links.
It provides great privacy and security, and it’s good for secure streaming, torrenting, and gaming. A VPN is an online app that also changes your IP address and encrypts your traffic — but it only does it once, which allows VPNs to provide much faster speeds than Tor. When you use the Tor network to access a site, your traffic is routed through at least 3 Tor servers, which are also called “relays” or “nodes,” and are usually run by volunteers. The Tor network is a privacy network that encrypts your traffic multiple times, making it completely unreadable. The Tor browser is a popular way for internet users to visit dark web sites. Onion sites aren’t really dangerous, but they could be when accessed through unfamiliar or suspicious links.
Alternative Anonymous Networks
In "safer" mode, JavaScript is disabled on HTTP sites, some fonts are disabled, and all audio and video won't run automatically, you'll have to click to play. To review security settings, click on the onion logo in the top left and select "Security Settings", which will bring up a slider offering a choice of the default of standard, or safer and safest. The latter choice is for when access to the Tor network is blocked, and you'll be shown a variety of circumvention techniques. While some can simply install and use the Tor browser like any other, there are a few complications for those in countries where Tor is blocked, on corporate or university networks where it's banned, or where more security is needed. The Tor browser spots such surveillance and opens each via a different circuit making the connections look like two different people, so the websites can't link the activity or identity if they login on one of the sites. That's done three times across a decentralised network of nodes called a circuit — the nodes are run by privacy-focused volunteers; thanks, you lovely people — making it difficult to track you or for sites to see where you're actually located.
Myth 4: The Dark Web Is Inherently Dangerous To Visit
Although they can’t see your browsing activity or Tor-encrypted data, your ISP can still see that you’re using Tor. Yes, Tor hides your IP, concealing it and making it difficult for anyone to trace your internet activity back to you. But fortunately, knowing how to use Tor Browser doesn’t require a PhD in computer science — it’s surprisingly easy and user-friendly. Tor Browser sends web traffic through an entry node (blue), middle node (green), and exit node (orange) to encrypt and decrypt traffic. Tor then transmits the multi-layered encrypted data across three layers of international proxies that make up the Tor circuit, which decrypt one layer each.

From this point onwards, you can enjoy complete anonymity and security while being able to access “.onion” websites and other dark web browser domains. The Tor browser provides access to “.onion” websites, which are Tor hidden services that you can only access through the Tor browser. The dark web refers to websites that are not on the regular internet but are instead hidden in a private network that is only accessible using specialized web browsers, such as the Tor Browser.
- But we are on the dark web, you can’t trust anyone, so there may be sites containing illicit content.
- Everything you do is protected by NordVPN, vital to accessing the dark web and enjoying it privately.
- For Android mobile devices, the official Tor Browser application can be found and installed directly from the Google Play Store.
- Also, you must log in or have a specific IP address or URL to access the deep web content.
What Is The Tor Browser Bundle?
Whenever you enter any domain into the address bar, your browser uses HTTP to find and request the data from the relevant server. Tor blocks JavaScript by default, but this addon lets you permit it for trusted sites. This addon allows you to control which sites can executive JavaScript and which ones can’t. We’ve explained how Tor protects your privacy by routing traffic through multiple servers.

This is a great resource for users looking to refer to old prices or job listings that have changed or are outdated. This platform is a time capsule with content, primarily web pages. Accessing tunnels is illegal and dangerous, which is why records of these “adventures” can only be found on the dark web. Read about the adventures of modern-day explorers who have made it their mission to venture into the tunnel network of huge American universities. It is one of the best sites on the dark web to find your favorite comics. You can access thousands of issues, from the most popular to the most niche.
With rising curiosity around hidden corners of the internet, many professionals wonder, “how to access the dark web” safely. Simply using Tor or visiting hidden services is not illegal in most places, it's a privacy tool. The Tor Project and security researchers emphasize that while Tor is resilient, it cannot guarantee absolute anonymity. In practical terms, dark web marketplaces, forums, and messaging services leverage this so both operators and users can interact anonymously. Tor onion routing passes your data through multiple relays, each decrypting one layer.
Because Tor hides browsing activity and blocks tracking, it’s used by whistleblowers, journalists, and others who want to protect their privacy online. With an encrypted and anonymous connection, Tor helps you access the unindexed part of the internet known as the dark web. Steer clear of forums, marketplaces, or content with illegal intentions. Plus, I don’t think that torrenting over Tor is secure, as some Tor servers can see your IP address, which is terrible for your privacy.