The operational capacity of darknet markets in 2025 demonstrates significant advancement in secure e-commerce. This competitive environment...
wpadmin
The website is available on the surface web and has a .onion site. Like any other site...
The market's interface is designed for efficiency, featuring advanced search filters and vendor review systems that allow...
Accessibility is maintained through secure onion addresses and multiple mirror links, which are distributed via specialized forums...
The stability of the platform's link directly influences the overall user experience. Users must obtain this link...
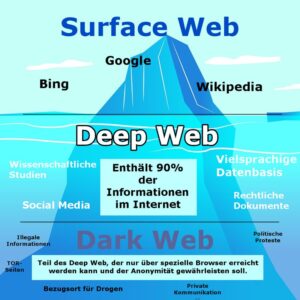
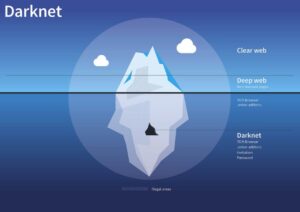
The process begins with aggregator sites, often called link directories, which provide verified lists of active market...
Keep in mind that the darknet environment is constantly evolving, so continuous research and updates are necessary...
These platforms function as sophisticated e-commerce ecosystems where vendors compete on product quality, purity, and service reliability....
A covert law enforcement seizure hasn’t been ruled out either. This often places the new market under...
Security researchers have been monitoring forums within the cybercriminal underworld to investigate the leading markets operating in...