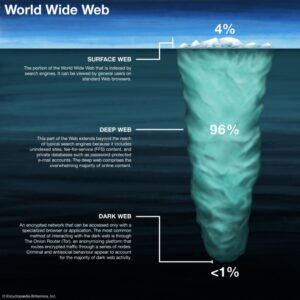
Approximately 57% of dark web content is estimated to be unlawful drugs, hacking, etc.. Monitor the dark...
wpadmin
Transactions typically use cryptocurrencies (Bitcoin, Monero, etc.), with most markets offering escrow systems or multi-signature wallets to...
Some fake sellers take your crypto and never ship what you ordered, or phishing sites that look...
If someone wants direct access to a server, a cPanel, or an email, this is the place...
The nightlife scene in Bangkok has a rich and evolving history that reflects the city’s dynamic cultural...
There are so many sources to purchase quality dark meat alone. Always check the ingredients to ensure...
The market is also known for its listings related to financial fraud, such as phishing tools and...
A June 2016 report from the Global Drug Survey described how the markets are increasing in popularity,...
With so many winter wonderland towns in Switzerland in December you are spoilt for choice and every...
At times of little wind, we import electricity from Sweden’s stored hydro power plants. In a social...