For the utmost privacy and security, combine Tor with a VPN connection. Essentially, you initiate a connection with the Tor network via the Tor browser first, followed by a connection to a VPN server. Routing your VPN traffic through a Tor connection is referred to as VPN over Tor. And because VPNs encrypt your traffic but are much faster than Tor, they’re also good for bypassing bandwidth throttling. And unlike the Tor browser that only secures the traffic that passes through it, a VPN secures all of your device’s web traffic.
Watch Out; Your ISP Could See You Using The Tor

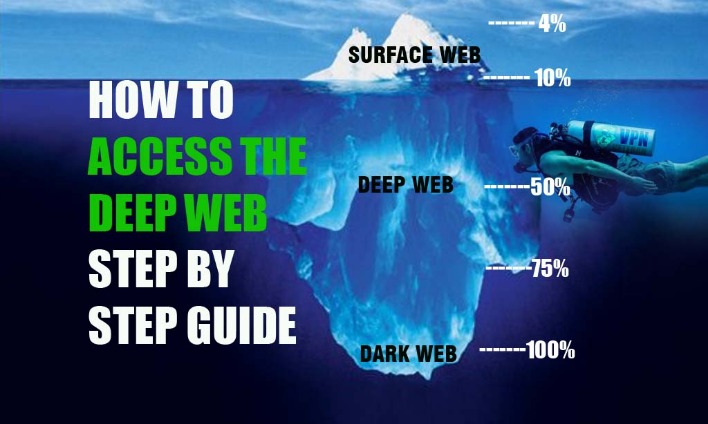
The Tor network’s principal benefit is that it routes your traffic through numerous servers, wrapping it in several layers of encryption. There are no laws restricting access to websites on the dark web. Because of their anonymity, dark web sites are breeding grounds for illegal activity and transactions. Web crawlers run the regular internet, scouring the web to discover newly published websites or pages in a process called crawling.
Moreover, NordVPN is a service that doesn’t store or log your search results. It encrypts your traffic at the entry node and changes your IP address. It offers top-of-the-line security and fast speeds for a smooth browsing experience on the dark web. A virtual private network (VPN) is a good way to mask Tor activities. It will encrypt your traffic and data so no one can intercept it.
NordVPN: The Ultimate VPN Service For The Tor Browser
Freenet is similar to I2P – you can only connect to sites within Freenet’s own network. Additionally, I2P doesn’t rely on hidden directories that serve as a resource for .onion domains. Meanwhile, Facebook also offers dark web access to their social network. Well-known news websites, such as ProPublica, have launched deep websites. Rule No.41 allows a federal judge to issue a search and seize warrant for any person who is using anonymity software like Tor.
Avoid fraudulent Tor-like browsers that compromise your online security. This hides your Tor usage from local networks, masks direct Tor connections, protects against network-level surveillance, and reduces the risk of being flagged for accessing privacy tools. Tor routes your traffic through a chain of relays to obscure your IP address. They’re part of the internet, but hidden from public search. Think of your email inbox, banking dashboard, cloud documents, subscription content, or internal business tools.
The peer-to-peer routing structure is more advanced, and it does not rely on a trusted directory to get route information. For a number of technical reasons, it’s much faster and more reliable than Tor. Both rely on a peer-to-peer routing structure and layered encryption to make browsing private and anonymous. Instead, I2P uses its own brand of hidden sites called “eepsites”. Due to all the nodes that your traffic passes through, Tor by itself significantly limits bandwidth. Some consider VPN over Tor more secure because it maintains anonymity throughout the entire process (assuming you pay for your VPN anonymously).
VPN-over-Tor (Limits And Niche Uses)
Such providers offer strong encryption and don’t store logs, ensuring all online footsteps are completely masked. What’s more alarming is the estimation that half of those visitors were connected to illicit activities. IOS is the only exception, leaving iPhone and iPad users without the option to go to this part of the internet. In short, it’s ideal for torrenting, streaming, and gaming. While you can visit the obscure part of the internet without a VPN, it’s better to go with one.
Many people see hacked information and stolen card data being sold on the dark web. The dark web also helps individuals communicate about or sell illegal items such as weapons, drugs, malware, etc. An easy way to find content on the dark web is to receive a link from someone who already knows about it. Lastly, the dark web is the portion of the deep web that is generally inaccessible and is much larger than the surface web.
Purchase Legal Goods Secretly
What should you do if your information is found in a data breach or you think it’s been leaked somewhere? When data brokers get hacked, the stolen data can include compromised credit cards, social security numbers, and other data, depending on what was exposed in the breach. To check, you can use dark web scanning or breach detection tools like Avast Hack Check or LifeLock Breach Detection to search for compromised data. By monitoring known dark web marketplaces, Avast BreachGuard will alert you immediately if and when your data is found. It’s possible to buy and sell illegal drugs, malware, and prohibited content in darknet marketplaces.
How To Access Your First Dark Web Or Onion Site
Your ISP won’t be able to see your Tor network activity. This means that all of your traffic, including your Tor Browser activity, is protected. However, be careful when using the Tor Browser to access the dark web. The NSA and FBI have been known to specifically target Tor users. Merely downloading, installing and using the Tor Browser is not illegal. Library Genesis offers a search engine for collections of books on such topics as computers, business, technology, and more.
Whonix is a privacy-focused operating system that routes all internet connections through the Tor network. It is an anonymity-focused network, though more niche than Tor. Built on Firefox, Tor Browser routes your traffic through the Tor network, anonymizing your IP and blocking trackers. These lists often include illegal or scammy sites mixed with useful ones. Despite the misconceptions, using one isn’t inherently illegal or dangerous if you know what you’re doing. If you want to be extra safe, routing your connection through a VPN and then accessing the dark web using the Tor browser provides more security than Tor alone.
- Another reason you don’t want to use the Tor Browser for your daily web browsing is that it draws attention to you.
- Although Tor is a sophisticated privacy tool, it has several disadvantages — some of which counteract its cybersecurity advantages.
- While the initial intent of Tor was to safeguard communication for military and government personnel, it quickly gained traction among privacy advocates and individuals seeking to evade censorship.
- From journalists and civil society organizations to regular individuals with online privacy concerns, Tor Browser users are a diverse group.
- A small part of the deep web is unindexed and requires a specialized browser to access.
- This is because the dark web is full of potentially dangerous content, and a VPN will help keep your identity and personal information safe.
Michigan THC Limits: Legal Consequences And Enforcement
Research what they offer and assess your privacy needs to make a decision about which dark web browser works best for you. There are alternatives to Tor, including the Invisible Internet Project (I2P), Lokinet, and Psiphon. While both tools enhance online privacy, they work differently. When using Tor, practice good security hygiene by avoiding suspicious links and using reliable antivirus software. Using Tor and the Tor Browser is considered relatively safe if you use the default security settings, but keep in mind that Tor does not provide end-to-end encryption.
Should I Use A VPN With Tor?
For example, a popular commerce site called Dream Market goes by the unintelligible address of “eajwlvm3z2lcca76.onion.” Dark web websites also use a scrambled naming structure that creates URLs that are often impossible to remember. That’s “a special-use top level domain suffix designating an anonymous hidden service reachable via the Tor network,” according to Wikipedia. Dark web websites look pretty much like any other site, but there are important differences. Only a tiny portion of the internet is accessible through a standard web browser—generally known as the “clear web”.
Older, shorter 16-character v2 .onion addresses were also used in the past, but these have been deprecated and are no longer supported by the current Tor network due to security vulnerabilities. While this may cause some websites to lose certain functionalities, the enhanced security is often considered a worthwhile trade-off, especially when navigating potentially risky parts of the internet. This masking is achieved through a sophisticated process known as onion routing, where web traffic is encrypted in multiple layers and channeled through a global, volunteer-operated network of relays.

Many dark websites are perfectly legal and safe to use and, in many cases, are better for your privacy than clear websites. Alternatively, users can connect in opennet mode, which automatically assigns peers on the network. Darknet mode allows you to specify who your friends are on the network and only connect and share content with them. Unlike Tor, however, it cannot be used to access the public internet. Additionally, Tor exit nodes are often blocked by websites that don’t trust them, and Tor over VPN can’t do anything about that, either.
Step 2: Install Hyphanet
A VPN encrypts your traffic before it goes into the Tor network. Though these browsers are effective at serving up dark web search results, the experience is reminiscent of browsing the web in the late 1990s. To access the dark web, you need an anonymizing web browser or any browser that supports the Tor network. The most prevalent illicit products are pharmaceutical and recreational drugs, followed by stolen data, online bank account credentials and credit card numbers. Keep in mind that in some regions like China and Russia, it’s illegal to use anonymizers.