Therefore, the dark web should not be considered synonymous with the entirety of the unindexed internet; rather, it is a specific, intentionally hidden segment prioritizing anonymity and privacy. Beneath this lies the “deep web,” a significantly larger segment encompassing content not indexed by these search engines. The “surface web” constitutes the portion indexed by standard search engines like Google and Bing, readily accessible to the average user. The fundamental principle behind Tor Browser’s operation is the separation of user identification from the routing of their internet traffic. Functioning as a modified version of the widely recognized Mozilla Firefox ESR, its core purpose is to facilitate access to the Tor network. Black Ops 7 turns its story mode into a live co-op service, with strict online rules that hit solo players hardest.
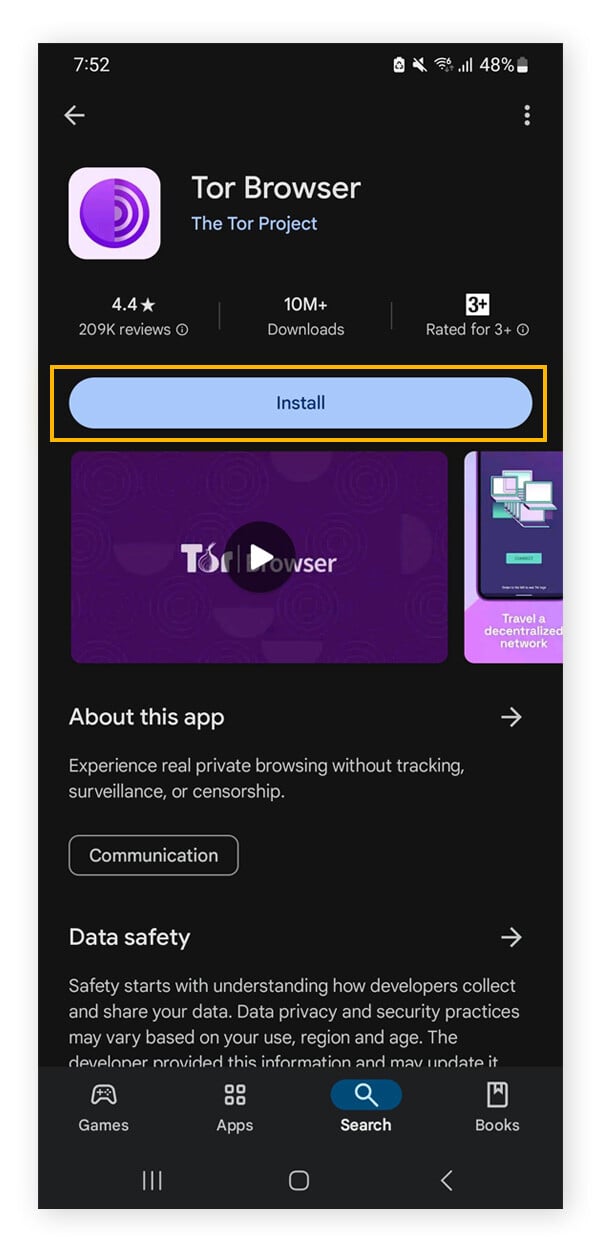
Is There A Tor Browser For Android?
In addition to being able to access any website you can in a standard browser, you can also access Dark Web URLs that end in .onion. This is the Deep Web because it’s not indexable by current search engines. Due to the anonymous and vulnerable nature of the Dark Web, it’s important to keep in mind certain things you should and shouldn’t do when accessing it.
Is It Illegal To Go On The Dark Web?
Combined with smart surfing behaviour and technologies like Tor and a VPN, even the darkest reaches of the internet may be securely traversed. Steer clear of forums, marketplaces, or content with illegal intentions. Designed to be hidden from conventional search engines like Google or Bing, the dark web is a portion of the internet.
If you manage not to expose your private information and avoid illicit activities, you can be sure everything will be okay. Such providers offer strong encryption and don’t store logs, ensuring all online footsteps are completely masked. What’s more alarming is the estimation that half of those visitors were connected to illicit activities.
Malware And Viruses
The many layers of an onion represent the multiple layers of encryption in the Tor network. In addition, all domains on the Tor network end with the top-level domain .onion (instead of .com). You wouldn’t want your email history available on the surface web and searchable by anyone. Deep web websites are the pages behind paywalls, authentication forms, logins, and passwords. Then, use data breach monitoring software to help find out if your personal data has leaked onto the dark web. Look for unusual domain formats, misleading content, and always cross-check onion addresses.
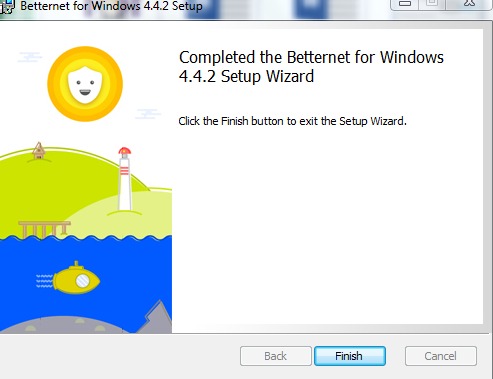
However, since it is so popular, you will find several versions of the program on the internet. You should also check that the VPN also features WireGuard protocol which is faster and more secure compared to older options like IPSec or OpenVPN. If you want to access the Dark Web safely, there are certain steps you need to follow to ensure your safety and privacy.
Tor Browser’s Levels Of Security
DefCon, ProPublica, the CIA, various libraries, and open-source software providers also feature in this area of the internet. To access a dark web resource, you will need to know its web address to the letter. It will normally take a while to connect because Tor — unlike other browsers — will route your traffic through different nodes. The Tor network is operated by thousands of volunteers worldwide who maintain the proxy servers that protect your identity. You should make sure you check the settings, and if you want a more secure experience, go for the "safer" or "safest" options, which also disable potentially dangerous website functionality, such as rogue JavaScript. ZDNET tested the best VPNs available based on speed, number of servers, security features, price, and more.
Only about 6.7% of global users use the dark web for malicious purposes, but it’s smart to be selective about the websites you access. Tor Browser gives you access to .onion websites that are available only within the Tor network. Tor offers a level of privacy and anonymity by routing your internet traffic through multiple servers, making it challenging for third parties to trace your online activities. These websites often have complex URLs that are not easily memorable, requiring users to utilize specialized search engines or directories to find them.
Accessing The Dark Web Securely In 3 Easy Steps
Buxyen is a privacy specialist dedicated to building and deconstructing secure digital environments. Each time you go online, you create a digital footprint that can be tracked. Think of the dark web as a hidden neighborhood on the internet. Using a VPN first hides your connection to the Tor network and gives you better privacy ultimately. Tor only anonymizes your identity through its routing; while your ISP won’t know who you are, they will see that you connected to the Tor network. A VPN conceals this access and will protect you from unwanted trouble.
Advantages Of Tor Over VPN

You only need the Tor browser to access the dark web. The correct top dark web browser download isn’t enough when it comes to safely accessing the dark web. Accessing your preferred part of the internet using a specific browser is straightforward.
The deep and dark webs seem like illegal places you should not visit. Let’s be honest, the dark web is infamous for its criminal marketplaces, where you can find almost anything illegal for sale. A small part of the deep web is unindexed and requires a specialized browser to access.
- Through the use of onion routing and many layers of encryption to conceal users’ names and locations, darknets provide secret and anonymous communication.
- In most regions, laws prohibit your Internet Provider from selling your data to third parties.
- Even in an era of increased online surveillance, the average person on the internet likely has too much to lose to bet on their safety for curiosity's sake.
- The encrypted data is sent through a series of network-based nodes called onion routers.
Past report of a potential security breach To access the dark web, you must have specialized software, such as the Tor Browser. Picture the internet like an iceberg.
Step 2: Install Hyphanet
Likewise, you’ll experience slower browsing speeds when browsing via Tor, as your requests get bounced through several servers before being processed. For example, we typed TechRadar.com into the address bar and accessed the website without any issues. Once complete, you can add Tor to your shortcuts menu for easy access.
It’s the side of the internet that’s used for transactions and conversations that need to stay anonymous. Sites on the dark web can contain potentially catastrophic pitfalls in the form of illegal activity, phishing links, financial scams, and malware infections. His articles attract a massive audience of over a million users every month. Damir is the team leader, product manager, and editor at Metaverse Post, covering topics such as AI/ML, AGI, LLMs, Metaverse, and Web3-related fields. Utilize strong anonymity mechanisms and take into account the ethical and legal repercussions to reduce risks. The inherent risks of using the dark web include being exposed to viruses, identity theft, scams, and contact with unlawful or immoral content.
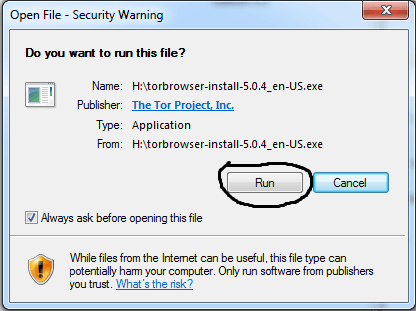
You can download the VPN app from the provider’s official website or your device’s app store. ExpressVPN is my top choice because it supports Tor traffic on all of its servers and works automatically without needing any additional configurations. Make sure you download the Browser from the official website (torproject.org). You need special tools to access the dark web, and the Tor Browser is the safest and most popular one.