Knowing these risks ahead of time can help you avoid the most common traps. A VPN adds protection before Tor, closing these gaps without breaking access to .onion sites. For most users, this configuration does more harm than good. It’s extremely rare and only useful in very specific cases, like if your VPN is only accessible through Tor. Most dark web leaks happen when users skip basic safety steps or reveal too much without realizing it. Screen dimensions are a known fingerprinting vector.
How To Protect Your Identity While Browsing The Dark Web
- The trade of exploits and zero-day vulnerabilities on the dark web poses significant threats to individuals, organizations, and even government entities.
- It uses PGP encryption to protect sensitive data and messages, and accepts payments via Monera and Bitcoin to keep you anonymous on this marketplace.
- DNMs have a limited life and may be shutdown suddenly, leaving users with unfulfilled orders and sellers with no means of communication.
- But products sold as ketamine, 2C-B and alprazolam were most likely to be completely substituted with other substances or new synthetic drugs.
- Staying informed about the risks, implementing robust cybersecurity measures, and reporting suspicious activities are essential steps in protecting oneself and contributing to a safer digital realm.
- It provides access to fake identity kits, spoofing services, and data scrapers.
Secure communication is vital to protect sensitive information and prevent interception by malicious actors. When venturing into the Dark Web to purchase credit cards, finding a reliable vendor is crucial to ensure a successful transaction. Engaging in such activities may result in serious legal consequences. However, be aware of fraudulent individuals who may try to exploit newcomers. Next, we will explore how to navigate the Dark Web and find reliable vendors to minimize these risks and protect against potential pitfalls. It is crucial to approach the Dark Web with caution and fully understand the risks involved.
Like other marketplaces, it also requires registration for new users and accepts payments in Monero. With a growing user base and expanding inventory, Vortex is positioning itself as an “all-in-one” darknet marketplace. All that one can expect from a deep web marketplace when it comes to anonymity and security.
Why We The North Marketplace Stands Out
– Read feedback from experienced Dark Web users or trusted individuals who have had successful transactions with the vendor. By reading feedback comments, individuals can understand if the credit card information received was valid, usable, and met their expectations. Engaging in illicit activities carries legal consequences, and there is no guarantee of the authenticity or usability of the purchased credit card information. It is essential to exercise caution, protect personal information, and prioritize online security at all times. Protecting personal information and ensuring online security should always be a top priority. Buying stolen credit cards is a criminal offense that can lead to hefty fines and imprisonment if caught.
For shopping of last resort, you need money of last resort – bitcoin, or possibly monero. By paying close attention to where adulterated substances were purchased, local drug checking services can help participants make more informed decisions to protect their health. If a drug checking service knows where a substance came from, they can decide whether it’s more appropriate to share any alarming results locally or online. “If we find something particularly nasty and it turns out you’ve got them from, you know, an overseas darknet, that’s kind of important for us to know,” she explained. “It’s a sensitive question to ask,” she admitted, “but I doubt many of those services are asking the question in the right way.”
Use Cryptocurrency For Transactions

Registration was mandatory to access the Silk Road (like most darknet platforms). All the payments were made through cryptocurrency, further enhancing marketplace anonymity. Some alternative links are available, providing access to the marketplace. The platform also cares about its users and uses PGP encryption and two-factor authentication to secure their data and communication. It uses PGP encryption, two-factor authentication, and OPTP authentication to ensure users’ security.
The Escrow Process

The dark web serves as a marketplace for individuals to acquire fake diplomas and certificates, deceiving others into believing they possess qualifications they do not. The dark web is known for being a marketplace where individuals can acquire falsified academic credentials, including fake diplomas, degrees, and certificates. This requires implementing robust data protection measures, educating employees about cybersecurity best practices, and following regulatory guidelines and compliance standards. They employ advanced techniques to track down cybercriminals, dismantle illegal networks, and raise awareness about the importance of data security.
Award Winning Cybersecurity
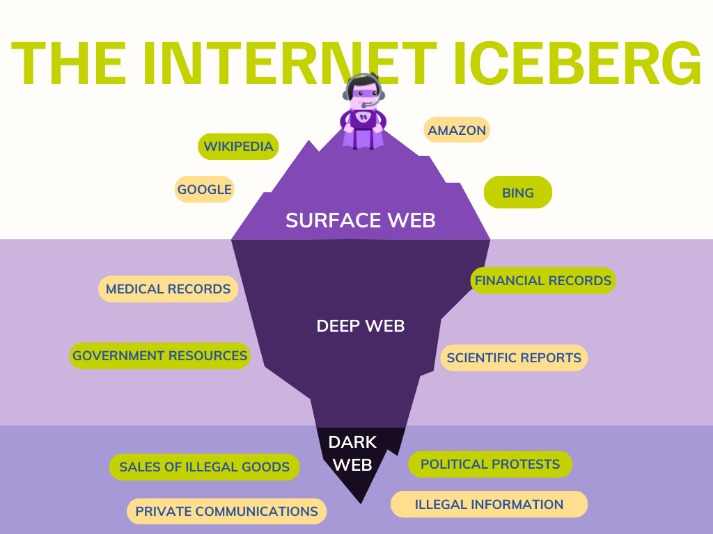
The deep web comprises any content on the web that is not indexed for search engines and that is accessed by password or encryption, or through gateway software. Finding a legit dark web marketplace can be tricky, but knowing where to look makes all the difference. While the dark web provides privacy and anonymity, it also comes with risks. Since these markets operate on the Tor network, they require .onion links that are not indexed by regular search engines.
How Effective Is Law Enforcement At Shutting Down Dark Web Marketplaces?
My advice to you would be to stick with the editor’s pick. Although content on the dark web is not as ‘indexed’ compared to the one on the clear web, you can still use search engines to find stuff. For this tutorial, I’ve used Universal.
And closely watch your credit report for when one of these cyber criminals does strike. The privacy affairs dark web price index says a social security number can go for $2 to $4. Your social security number can be bought on the Dark Web for less than you'd pay for a carton of eggs.
But human trafficking, illegal pornography featuring underaged victims, money laundering, and assassinations are also examples of the darkest corners on the dark web. To access the dark web, you’ll need a specific set of tools – more about that later in the step-by-step section. Unlike the surface and deep web, you can’t access the dark web via a standard or specialized search engine. The deep web contains sites and pages that are often prevented from being indexed by search engines and contain unlinked content.
This obviously come with certain risks if it gets into wrong hands. It has been seen that certain stores or vendor shops have opened up offering solely fake currencies. There are a lot of .onion links on the tor that lets you buy counterfeit currencies.
Often written as RussianMarket, this is the largest marketplace for stealer logs. STYX is a great example of a ‘new model’ market with a searchable structure and trusted vendor processes, which helps buyers quickly filter for fresh data. Unlike older drug-oriented markets, STYX looks more like a specialized cybercrime exchange than a bazaar. Its listings focus on stealer logs, initial access and financial credentials, making it highly relevant for financial security professionals.
Researchers say the internet is a surprisingly common method of obtaining fentanyl, an opioid that is now responsible for more overdose deaths than heroin or prescription painkillers. (I was connected to this man through a researcher on the condition of anonymity, out of concern he would be jailed if discovered.) To get extremely potent opioids, users turn to the dark web—and sometimes, Google. Some countries lack comprehensive cybercrime laws, complicating international efforts to combat dark web activities. States may have additional statutes addressing specific cyber activities, creating a layered legal environment.