It maintains a very strict level of user verification and integration with an official Telegram account to...
Uncategorized
The overall aim was to estimate the size and scope of the trade in firearms and related...
Unlike a credit card, a debit card is connected directly to your checking account, allowing fraudsters to...
The most common darknet software is the free and open-source Tor, short for the Onion Router. The...
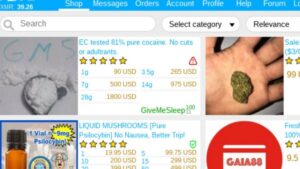
A February 2016 study from researchers at King's College London gives the following breakdown of content by...
Tumbled bitcoins are bitcoins that have been mixed with other bitcoins to obscure their transaction history. Other...
The invisible web is made up of data and information that is not indexed and cannot be...
Understanding how data gets stolen is the first defense against it. The dark web offers a marketplace...
This comprehensive guide will dissect the key backmarket alternatives, comparing their business models, warranties, and overall customer...
AlphaBay and other markets of this period implemented multisignature transactions, stronger encryption protocols, and improved escrow systems....