Threat actors in the dark web have been known to post about selling or sharing finance-related data, as discovered by SOCRadar in the first eight months of 2022. Digital Risk Protection Threat Intelligence Dark Web Monitoring Cybersecurity Platforms Security Tools Why Threat Intelligence Platforms Matter Now Traditional firewalls can’t protect against stolen passwords. By leveraging automated dark web monitoring, organizations can mitigate risks, and take preventive measures before the leaked data is exploited.
Our analysis showed that 42,310 of these stolen cards were unique or first observed in the Argos intel collection. Based on the intelligence Cyberint gathered during our investigation, we discovered that the threat actor or group has been active in carding forums as far back as last year under the profile “B1ack,” formerly known as “blackclub,” and often referred to by users as “king.” Password managers like LastPass and Apple's Keychain show if your passwords have been compromised or overused by scouring the black market and alerting users how many times their passwords appear. Counterfeit products spike around Black Friday and Cyber Monday, especially on online marketplaces and in third-party listings. Lastly, remember that the traditional web offers countless legitimate ways to engage in online transactions and protect personal information. By doing so, you can contribute to mitigating the impact of these illegal activities and help protect innocent individuals from falling victim to financial fraud.
Protecting Yourself From Dark Web Credit Card Fraud
FTx Identity provides the critical verification layer needed to protect against the sale and misuse of personal data found on the dark web. Businesses can strengthen security with 2-factor authentication to prevent customer accounts from being taken over by thieves. There are many techniques to prevent identity fraud that businesses and individuals can use. Instead, stolen data is permanently accessible on the dark web and can be bought, sold, or used in various ways. Financial loss, harm to one’s credit score, and a great deal of stress and frustration as they try to fix the problem can all be experienced by identity theft victims. The cycle is complete when the stolen data is used to generate profit or cause harm.
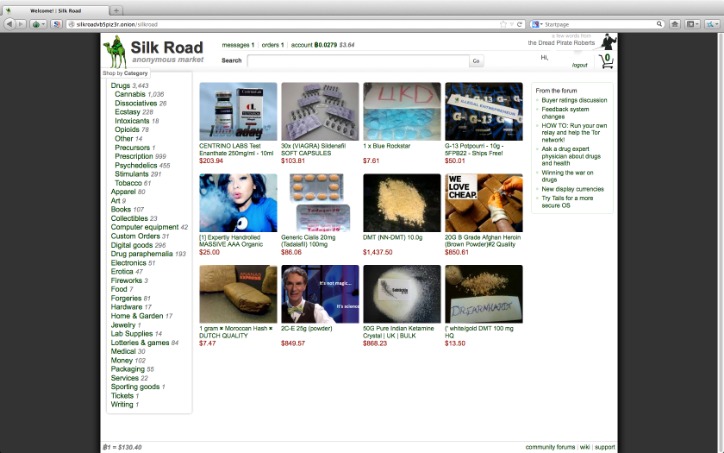
(Also, some users of these sites will offer to sell you bitcoins via Paypal so you can skip the two banking steps above and jump right into buying your goods; there is of course no guarantee that you will receive your bitcoins after giving up your cash.) All users can send data via Hidden Tor email servers, or ship physical items like drugs and weapons with the US Postal Service to prevent any searches without a warrant. We have touched on Tor two or three times to protect your identity while online, but Tor includes other functions. Clearly anyone engaging in black market activity wants to remain anonymous.
Current Best Darknet Market
Draghetti pointed out that a previous such promotion was used by the BidenCash credit cards site to promote the marketplace to a wider criminal audience. It is illegal and unethical to engage in activities that exploit stolen credit card information. The online black market thrives because stolen data can be resold repeatedly, multiplying financial damage long after the original breach. After all, cybercriminals can use the cards to buy items, extract the cash from the account, or just continue to charge the card itself until the bank realizes that the transactions are fraudulent.
Products & Services
Manual monitoring of the dark web is inefficient and risky due to the sheer volume of data involved. This early detection allows organizations to identify and respond to threats quickly, reducing the chances of unauthorized access, financial loss, or damage to brand reputation. In addition to its emphasis on stolen credentials, 2easy Market offers a variety of cybercrime tools, such as hacking services, exploit kits, and other resources for conducting cyberattacks. The market is known for its extensive product listings and reputation system that helps buyers evaluate the reliability of vendors.
Require multi-factor authentication for high-risk transactions, but it needs to be implemented intelligently. Instead of storing actual card numbers, each card should be converted into a unique token. Using a layered approach helps distinguish genuine fraud from false positives. They look at everything from how quickly a customer fills out payment forms to whether their IP address matches their billing location.
On some black market websites, these tools are even sold as “fraud-as-a-service” packages, complete with user manuals and customer support. One of the fastest-growing threats, synthetic identity fraud combines real and fake details to create entirely new identities. This practice, known as credential stuffing, has become a key pillar of the global black market data economy. Criminals test them with small purchases before making large transactions or selling verified cards to others for profit. Stolen card numbers are still a dominant currency on the black market access networks.
Cyble Titan Endpoint Security
In May 2024, Ticketmaster faced a significant data breach affecting millions of customers. In April 2024, a data broker company, National Public Data, suffered a catastrophic breach, exposing 2.9 billion records. It features a unique site design unlike any other market yet is still intuitive and easy to use. Kingdom Market is a newer darknet market that has been around since April 2021 but was only recently vetted for listing on Dread, the pre-eminent forum for markets on the dark web.
What To Do If My Info Is On The Dark Web
When Torrez closed in December it was one of the largest English-language marketplaces in the world selling drugs, hacking tools, counterfeit cash and criminal services. It's also the latest in a growing list of criminal marketplaces to have voluntarily retired in the last six months. If someone wants direct access to a server, a cPanel, or an email, this is the place to go.The market is in English and features a massive catalog with over 800,000 illegal products. Because everything here revolves around stolen accounts and access credentials.
A Criminal Underground With Certain Limits

Initially, this specific marketplace started out by leaking thousands of credit cards. As reported by Bleeping Computer, in an effort to attract cybercriminals to its platform, the hackers behind ‘BidenCash’ have distributed the details of 1,221,551 credit cards. White House Market’s most lasting impact will likely be establishing a higher industry standard for operations security and customer service among dark net market platforms, making transactions harder to trace and providing a smoother experience for online black market users. Holders of any credit cards, whether you know if they have been compromised or not, are advised to monitor bank statements for any suspicious or unusual activity.

If you ever decide to explore the dark web, protecting your identity is crucial. Some markets are invite-only or have strict registration rules to keep out scammers and law enforcement. One of the most common is the exit scam, where a marketplace suddenly disappears and takes everyone’s money with it. Just visiting the dark web, or using a tool like Tor, isn’t illegal in most countries. Some are looking for illegal stuff they can’t buy elsewhere, like drugs or counterfeit documents.
- FTx Identity provides the critical verification layer needed to protect against the sale and misuse of personal data found on the dark web.
- Torzon offers a premium account option for additional benefits and is valued at approximately $15 million, accepting payments in Bitcoin (BTC) and Monero (XMR).
- They use data breaches, phishing, and skimmers.
- More bogus credit card data, personal information, and documents were sold in 2021 compared to 2020, while products, like hacked cryptocurrency accounts and web services such as Uber, are more available.
The ease of access and navigation of Telegram carding groups is a major concern, as it allows cybercriminals to easily buy and sell compromised payment card details. These groups often originate from leaked credit card credentials, which have become a common phenomenon, particularly in the past months. This financial loss can occur through unauthorized charges, account takeover, and identity theft. These checkers are often offered and sold on the dark web, and are complimentary tools that individuals and organizations use to verify credit card information. Card checkers are tools used by threat actors to verify the validity and authenticity of credit card information they purchase on the dark web. Such type of data is likely to have been compromised online, making it a red flag for would-be fraudsters.
- Threat actors in the dark web have been known to post about selling or sharing finance-related data, as discovered by SOCRadar in the first eight months of 2022.
- Regular account checks and strong passwords help.
- Alex Herrick knows the dangers of online fraud.
- Christin says this moral stance underscores a truism for how black markets exist amid the threat posed by law enforcement.
- It features over 40,000 listings including narcotics, counterfeit items, hacking tools, and stolen data.
Stolen credit card details are often sold on platforms and websites dedicated to, and branded as, carding websites. Unlike other types of stolen data—such as email lists or personal information—carding exists as its own distinct niche within the cyber crime ecosystem. The leaked data from the BriansClub hack showed that stolen cards from U.S. residents made criminals about $13 to $17 each, while those outside the U.S. sold for up to $35.70, Krebs reported. Carding forums — where cybercriminals chat about stealing card information, share tips for how to hack into websites and more — and marketplaces, where card data is actually bought and sold, are prolific on the dark web, Thomas says. Most stolen card details end up on the dark web marketplace for a quick profit, and this can happen before you even know about it.
How Xanthorox Helps Cybercriminals Generate AI-Powered Malware
When a hacker writes up new malware, steals a database, or phishes someone for their credit card number, the next step is often toward dark net marketplaces. Criminals use stolen credit card data to make fake purchases. Discover the pros and cons of using credit cards or card for purchases, including benefits and risks, to make informed financial decisions. The threat actor's marketing strategy involves leaking a large number of credit cards to attract potential clients from hacking and cybercrime forums. Magnetic stripe data dumps on the dark web include raw credit card data, such as bank account numbers and account balances. Stolen credit cards are often used to make purchases at specific sites that don't have protections against fraud.