Many dark net sites do not undertake the necessary measures to protect users like most websites on the surface web. Unfortunately, others are fake and fraudulent websites that exploit the reputation of the dark web to con people. With rising online privacy concerns in the current digital age, the Tor network’s anonymity is becoming essential.
Using a reliable VPN provider helps keep you safe when you access marketplaces on the dark web. The layers of encryption hide your data and activity from snooping eyes. Monitoring dark web markets is crucial, no matter if you are a business or individual, as you can then proactively identify and mitigate potential breaches and cyber threats. As these marketplaces keep changing, it is critical to stay on top of the main platforms on the dark web worth monitoring. Therefore, you must know how to access dark web marketplaces safely (covered later in this article). The dark web marketplace is an online marketplace where you can buy and sell anything.
The Top 11 Dark Web Links To Explore

Awazon Marketplace is the leading dark-web marketplace that claims to provide a secure destination for anonymous trading. Smartmixer.io mixes your funds with the funds of other people using the pooling method, making it hard to trace the transaction. But, if the blockchain does keep a record of transactions and it is easy to track you with your coin address, how does Smartmixer.io keep you anonymous? This is largely due to harmful elements in the dark web, and Ahmia contains certain questionable and largely illicit links. It also provides insights, helpful statistics, and updates regarding the Tor network.

OnionName — Buy Readable Onion Domains
Ahmia also discourages access to illegal content and promotes safer internet practices. Though you likely won't remember the addresses of onion websites, you can find these URLs on various websites on the internet. While the Tor network was not created for illegal activities, as it's harder to trace websites to their physical location, cybercriminals have also adopted it to host their websites.
The platform also supports freedom of expression by granting access to censored or restricted information, making it popular among activists, journalists, and individuals living under oppressive regimes. Never share personal information, avoid clicking suspicious links, and consider using additional layers of privacy like a VPN. Cybersecurity experts should pay close attention to these trends, as they often indicate emerging threats and profit-generating tactics among the cybercriminal forums. Here are some of the now-defunct dark web markets that were notorious for cybercrime.
Are Dark Web Links Illegal?
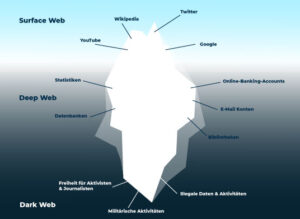
The dark web hosts a variety of content, including anonymous forums, marketplaces selling illegal goods (like drugs and weapons), hacking services, and information stolen in data breaches. Tor browser is generally used to access Darknet content because it offers users high anonymity and security. These onion domains are not indexed by search engines, so users can only access and explore the deep web through special software called “The Onion Browser” as TOR. The deep & dark web is the hidden part of the internet that contains illegal information, services, and web pages not indexed by the Google search engine. By providing specialized tools and services, our company can help users protect their privacy and anonymity online while accessing the information and services they need.
You can access almost any published paper that would have otherwise been hidden behind a paywall. Sci-hub is a helpful dark web platform for those looking to access important research blocked by a paywall. You can easily find what you are looking for, even links to hidden dark web rooms.

The blog contains tons of useful guides about how you can avoid online surveillance. This is a blog with cybersecurity tips created by the Electronic Frontier Foundation (EFF), a popular non-profit that specializes in digital privacy. It’s a good choice for people in risky situations and censored countries.
Should I Only Use A VPN To Access The Dark Web?
Although ProtonMail also exists on the clear web, accessing it via Tor provides an extra layer of privacy if you don’t want to leave a trace of you even using ProtonMail. The service retains no copies of any data that passes through a ProtonMail account. ProtonMail is an email service that uses end-to-end encryption, making your email accessible to you and only you. Although profiting from pirated copyrighted material is unethical and illegal, there are some exceptions to using copyrighted material, such as a “private study” provision under UK law. Of course, bypassing paywalls is ethically questionable and may be illegal in some jurisdictions. On it, people can ask any question; no discussion will be taken down or moderated.

Why Use The Hidden Wiki Instead Of Google?
It’s a nonprofit agency whose main purpose is to develop and research online privacy tools. People often refer to dark web urls as the seedy underbelly of the internet. If you want to find out how to access dark web links and how to do it safely — keep on reading. Be sure to share and bookmark this current list of darknet websites.
Online Best Dark Web Search Engines For Tor Browser
This includes sites with publicly accessible content, such as news portals, blogs, and social media platforms. This specialized web browser is designed to route your internet traffic through the Tor network, which anonymizes your connection by bouncing data through multiple volunteer-operated servers around the world. The Tor Project’s official onion site offers secure downloads of the Tor Browser and developer resources, helping users access and contribute safely to the Tor ecosystem. Daniel’s Hosting specializes in anonymous hosting services optimized for Tor sites, providing secure environments and DDoS mitigation. The ProtonMail Onion site offers the same encrypted email services trusted globally, now accessible anonymously through Tor. Dark web marketplaces remain the backbone of many users’ dark web experience, providing anonymous platforms for buying and selling goods and services that range from digital products to physical items.
New York Times
Because it’s not as safe as Tor over VPN. Well, VPN over Tor is basically its opposite – instead of going through the VPN first, the signal passes through the Tor network, before going through the VPN. Not very safe, but it’s still useable. Well, it’s really not that complicated – using the Tor over VPN method means connecting to a VPN service before using the Tor browser. This multi-layered redirection ensures your actions leave no trace, offering a high level of anonymity. By using Tor, and especially in combination with a VPN, your internet signal is encrypted, making it invisible to your ISP.
A reliable VPN encrypts your traffic before it enters the Tor network, preventing surveillance from your ISP or malicious actors. BlackCloud offers encrypted file storage specifically optimized for the Tor network. Some content can be unmoderated, though, so it’s worthwhile to be careful while using this platform. This service helps protect your primary email when signing up for .onion services. The website’s articles focus on digital rights, surveillance, and security research.
Browse The Web More Safely
- This means you will get a VPN’s security and enjoy the anonymity of the Tor network simultaneously.
- You have successfully accessed DuckDuckGo on the Tor Browser, enabling you to search the depths of the dark web while preserving your privacy and anonymity.
- If you want to be extra safe, routing your connection through a VPN and then accessing the dark web using the Tor browser provides more security than Tor alone.
- By contrast, accessing the Hidden Wiki through the Tor Browser offers anonymity and minimal data exposure.
- The search results from DuckDuckGo will be for websites on the regular web, which you still visit through Tor.
The website has a clean and easy-to-use user interface without any innovations that won’t trouble users. Moreover, this shop provides detailed statistics about each user profile on the platform, giving users a better idea of the vendors for the buyers and vice versa. To prevent users from DDoS attacks, it provides personal marketplace domains to high-volume buyers and sellers.
Ahmia is one of the search engines intended to get into the Tor browser. But it’s junk to death with ads; even their homepages on the TOR networks and the consistent net are overflowing with ads. Most frequently, Google cannot find the whole shebang on the Web, so you need special search engines to find information that is not easily available. Tor and tails are two tools that help you to protect your anonymity online. Hence, it’s essential to be careful when accessing the deep web and only use it for the rightful purpose. Every server in the Tor network decrypts and re-encrypts your internet traffic before passing it to the next server.
Tor Browser is a specialized web browser with innovative open-source technology that uses smart methods to safeguard your online anonymity. Tor is a free and open-source web browser that intends to secure the user’s anonymity and privacy online. So, it’s necessary to use Tor before accessing the Deep web. The Tor Network is a decentralized server network that encrypts and redirects internet traffic to secure the user’s privacy. Tor Browser is just a VPN that lets you access the Deep web while keeping your identity secure and anonymous. Browsing the deep web URL and dark web is a secure process, but you must have trustable security software that gives you extra mileage and anonymity.