It also uses global law enforcement networks, like Europol, to combat cybercrime threats. “The FDA is committed to continuing its work to disrupt and dismantle the illegal sales of drugs on the dark web, where such sales far too often have tragic consequences,” said Chad Menster, Deputy Director of the Food and Drug Administration’s Office of Criminal Investigations (FDA OCI). "By cowardly hiding online, these traffickers have wreaked havoc across our country and directly fueled the fentanyl crisis and gun violence impacting our American communities and neighborhoods. But the ease and accessibility of their crimes ends today," said FBI Director Kash Patel. “This historic international seizure of firearms, deadly drugs, and illegal funds will save lives,” said Attorney General Pam Bondi.

How To Find New, Active Dark Web Links
The vendors of the dark web hand over the packages to their shippers to send them. The DNM vendors need a list of people to find, so they look at the sex offender registry and find the worst sex offenders, Level 3, to use their names as the return address. Most vendors don't need to use concrete or steel like the cartels do when shipping large amounts.
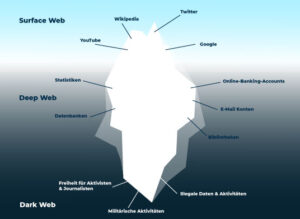
You can access it with regular web browsers and search engines. It is easily accessible by the general public and requires no special configuration. Instead, you need a specific configuration, software, or authorization, such as Tor, to access it. These sites aren’t just important resources; they’re like lifelines used to serve readers living under oppressive regimes. Everything you find on the dark web is not necessarily illegal.
Marketplaces For Everything Illegal
Regular perimeter checks are important to locate any unusual activity around the operational area that can get the darknet vendors arrested. The deep web drug vendors mostly carry their flash drive with stored keys in case of emergency. To avoid suspicion and detection, darknet vendors employ stealth shipping methods. Pretty Good Privacy (PGP) encryption is widely used by darknet vendors to secure their communication and protect sensitive information. It allows users to access websites anonymously by routing their internet traffic through a series of volunteer-operated servers.
These stolen cards can be used for financial gain through unauthorized charges, account takeover, and identity theft. These platforms are hubs for cybercriminals to buy and sell compromised payment card details. Carding groups and channels are easy to navigate, making them a growing threat in the dark web. Such type of data is likely to have been compromised online, making it a red flag for would-be fraudsters.
- I also included instructions on how to access the dark web, and outlined how to stay safe when browsing dark web links (the dark web is also home to many scams and malicious sites).
- You will need the Tor browser to access these links and the other (hidden) internet, the dark web.
- Even if someone accidentally stepped on the box and tried to look inside, the visual barrier would not reveal its contents.
- Consider using a password manager to securely store and generate complex passwords.
- This scam can result in significant financial loss for both buyers and legitimate vendors.
The site is accessible via both Tor and the clear web, and its layout closely resembles that of Abacus Market, which makes navigation very user-friendly.Notable features include an automated carding shop, an escrow system for manual orders, and a dashboard that displays balances in both BTC and Canadian dollars (CAD). These campaigns helped them gain users and redirect traffic after attacks such as DDoS.With an easy-to-use interface, a vast amount of data, and constant updates, BidenCash has become a favorite among cybercriminals involved in identity theft and financial fraud. One of the most notable occurred in 2022, when 7.9 million credit card records were released. Add in easy access and a vast inventory, and it’s clear why FreshTools remains highly active in 2025, even partly operating from the clear web. There are RDP accesses, SMTP logins, SSH credentials, fake pages, and even fraud tutorials.
Mastering Credit Card Cards: Features, Fees, And Rewards
What’s the difference between classic marketplaces and data stores? Launched in 2023, STYX focuses on financial crime, providing stolen credit card data, hacked bank accounts and access to various cryptocurrency laundering tools. Security researchers have been monitoring forums within the cybercriminal underworld to investigate the leading markets operating in 2026. Some dark web marketplaces even host content that’s not just illegal but extremely harmful, so it’s really important to understand the risks before diving in.
Visiting the links from specific questions may be a bit safer. Its mission of open access is debated within academic and publishing communities. It aims to advance research on terminal illnesses like cancer with access to unbiased scientific publications. Sci-Hub is a massive database that eliminates the barriers to getting scientific knowledge.

Such launches were not always a success; in February 2014 Utopia, the highly anticipated market based on Black Market Reloaded, opened only to shut down eight days later following rapid actions by Dutch law enforcement. It has been considered a "proto-Silk Road" but the use of payment services such as PayPal and Western Union allowed law enforcement to trace payments and it was subsequently shut down by the FBI in 2012. In 2012, it was closed and several operators and users were arrested as a result of Operation Adam Bomb, a two-year investigation led by the U.S. A darknet market is a commercial website on the dark web that operates via darknets such as Tor and I2P.
Are Small Businesses At Risk By Outsourcing Parts Of Their Operations?
However, remember you must use the Tor browser to access them. It is possible to navigate the dark web even though it doesn’t host user-friendly onion search engines. If you choose to visit the dark web, you must take the necessary measures to protect your privacy and security. Some of these sites are very helpful (but unseen as Google doesn’t show them), while others are just for fun. This article lists some of the best dark web websites you can visit securely.
In furtherance of Operation RapTOR and in their first action as a JCODE member agency, the Office of Foreign Assets Control (OFAC) additionally sanctioned Behrouz Parsarad, an Iranian national, for his role as the founder and operator of Nemesis Market following seizure of the market. These actions provided investigators across the globe with invaluable leads and evidence, strengthening the ongoing fight against cybercrime and illicit activities on the darknet. Led by Europol’s European Cyber Crime Centre Operation RapTOR united the FBI-led JCODE team — comprised of ICE HSI and law enforcement partners from the United States, Europe, South America, and Asia — to disrupt fentanyl and opioid trafficking, as well as sale of other illicit goods and services on the Darknet.
Elite Cyber Veterans Launch Blast Security With $10M To Turn Cloud Detection Into Prevention
- Blockchain.info (now Blockchain.com) is a popular cryptocurrency wallet and blockchain explorer service (one of the first sites to launch on the dark web).
- The best thing is to actually understand how to find the fresh, new links.
- However Black Bank, which as of April 2015update captured 5% of the darknet market's listings, announced on May 18, 2015, its closure for "maintenance" before disappearing in a similar scam.
- PGP allows for the encryption of messages, ensuring that only the intended recipient can decrypt and read the content.
- The indexed data is then analyzed and correlated to identify potential dark web threats, data breaches, or other relevant information.
- Cybercriminals increasingly use Telegram as a platform to facilitate illegal transactions due to its enhanced privacy features and encryption.
Lunar has the capability to oversee these activities across a variety of sources, including instant messaging platforms like Telegram and traditional dark web sites like those on Tor and I2P. Cybercriminals increasingly use Telegram as a platform to facilitate illegal transactions due to its enhanced privacy features and encryption. For example, 70% of police departments in the UK plan to invest in AI technologies for law enforcement by 2023, indicating a growing pattern of AI adoption in law enforcement across different countries. Recent articles claim that 63% of law enforcement agencies in the United States use AI in some form. These regulations encourage businesses to track dark web activities to prevent stolen data from being sold or misused.
Hidden Answers
Reliable vendors ensure their product descriptions are accurate and provide value for the buyer’s investment. Established vendors with a track record of successful transactions are more likely to be reliable. However, amidst the sea of sellers, it can be challenging to identify trustworthy vendors.
The lifeblood of these virtual bazaars pulsates through the veins of its vendors. Venture deeper into the underbelly of the dark web, where bustling marketplaces hum with activity and cryptic figures pull the strings. We have delved into the intricate workings and complexities of these secretive marketplaces, revealing the risks and implications they pose. Our exploration of darknet market operations has shed light on the hidden world of illicit online trade.
Contributor: Why Do So Many People Cut Ghislaine Maxwell So Much Slack?
Anyone who wants automated Al and ML-based web monitoring features in their dark web security solution must try this tool. Part of its service is the threat intelligence solution that automatically scans and updates the databases with new information collected all around the web. The system automatically scans dark web marketplaces, forums, and social media sites to check whether the information is sold or displayed on an open free list. It inspects underground marketplaces, Telegram, IRC, Tor, I2P pages, forums, and paste sites and sends alerts to notify the affected organizations.
Cobwebs Technologies Web Investigation Platform
To understand how dark web marketplaces work, you must look at the structure of listings. Fraud, scam attempts, or poor service can lead to immediate bans, which is why vendors protect their reputation aggressively. Marketplaces intentionally limit accessibility to maintain operational security. A defining feature of how dark web marketplaces work is their use of layered anonymity. To understand how dark web marketplaces work, you have to recognize that they operate within an underground economy defined by trust, anonymity, and incentives. In this article, we break down how dark web marketplaces work, how they are built, who uses them, and why they continue to thrive.
It specialized in narcotics, stolen data credit cards, credentials and contraband. By 2017 it boasted 200,000+ registered users and 40,000+ vendors, with roughly 250,000 drug listings and 100,000 non drug listings. These hidden markets promise anonymity, but in practice, users often slip up. These markets use cryptocurrencies and encryption to hide, but law enforcement’s growing technical skills have repeatedly broken them open. ZeroFox combines AI-powered dark web monitoring and human intelligence provided by our DarkOps team. Monitoring the dark web can help enterprise security teams anticipate and counteract upcoming cyber attacks, or detect evidence of prior attacks and take action to minimize the damage and prevent further distribution of stolen data.
Accessing blocked content can result in being placed on a watch list or imprisonment. Government authorities across the globe are taking over many Tor-based sites. Unfortunately, others are fake and fraudulent websites that exploit the reputation of the dark web to con people. Some services are genuine; you can get what you want at an agreed fee. Many services that are allegedly offered on the dark web are scams. Here are some of the common dark web dangers that users can face.