
While many people use the dark web for legitimate reasons like privacy (such as journalists or activists in oppressive regimes), it’s also known for illegal activities. First, you need to know how to access the dark web, and once you’re in, you can’t just perform a normal Google search. While it offers access to a world of hidden knowledge, it also poses significant risks. No, while many illegal activities occur on the dark web, there are also legitimate uses, such as privacy-focused forums and information networks. Tor is an acronym for The Onion Router, and it was created by the US Naval Research Laboratory in the mid-Nineties. The US has the most Tor users (19% of the total number) with theUK in seventh place (3.4%).

Haystak offers an uncensored yet privacy-focused search engine experience. Its indexing is relatively shallow compared to other uncensored engines, meaning many dark websites remain undiscovered or unlisted. Ahmia filters its results to block illicit content and harmful sites. For example, sites with high uptime or community upvotes may be prioritized in search results.
What To Do If You See Something Illegal
To prevent detection, the program runs user data via a tiered stream before allowing access to the dark web. Tor and I2P are the two commonly used tools for accessing the dark web to provide anonymity. Also, you must log in or have a specific IP address or URL to access the deep web content. It means you cannot access websites on the dark web with regular browsers like Firefox or Chrome.
The Role Of Dark Web Monitoring Services
I use separate Tails instances for journalism vs. research to avoid cross-contamination. Enable heuristic scanning to catch dark web-specific malware (e.g., ransomware from unfiltered Torch links). Use default bridges or consult torproject.org for custom setups in censored regions. However, privacy risks (e.g., AI tracking, regulatory overreach) demand vigilance. By 2030, ethical debates over content moderation could split the ecosystem, with some engines (e.g., Torch) remaining unfiltered and others (e.g., NotEvil) adopting stricter policies.
Data Breaches And Scams
The Tor network consists of a series of volunteer-run servers that route internet traffic through a series of encrypted tunnels. The Tor Browser routes your internet traffic through a network of servers, making it difficult for anyone to track your online activity. The Tor Browser is designed to protect your privacy and anonymity when using the internet. The dark web in 2025 still holds power, but only for users who browse smartly.
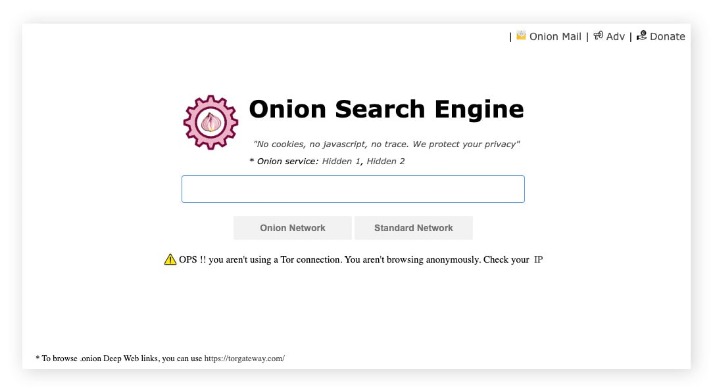
This open model, however, presents a significant risk because malicious or unverified links can easily appear in search results. This is a huge risk, as the Tor Browser disables JavaScript by default to protect users from being "fingerprinted" or de-anonymized. Users can filter searches to focus on a single network or see blended results. Queries frequently return broken .onion links or irrelevant listings.
What Is The Hidden Wiki?
Secondly, the security threats from evil entities are amplified to a level where unprotected surfing is like taking a risk with your life. Although the dark web is mostly linked with illegal drug trades and cyber crime it still plays a vital role for activists, whistleblowers, and individuals in need of safe communication in restrictive areas. Communication among devices in computer networking is primarily dependent on how systems recognize and get to each other.
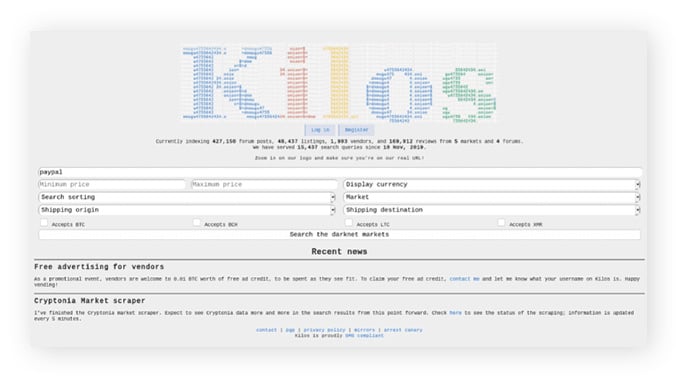
It offers a search-feature with filters such as price-range, display currency, shipping source and destination, payment options (for the Drugs) etc. Kilos breaks the Deep Web barriers and ventures into the Darker side of the deep web. It also claims to have over 1million pages indexed in its database, which I suppose is enough for most of us. It’s also extremely simple, there’s the logo, and the search bar. Although for some reason the search result only shows us the URLs, and last update date but no description of the site for most results.
This will make sure you can’t be hacked/traced as easily, and that you can’t be legally troubled for unconsciously landing on something illegal. At times, I’ve clicked on a link thinking it’s a harmless, informative site. You can find Ahmia on the dark web at the address juhanurmihxlp77nkq76byazcldy2hlmovfu2epvl5ankdibsot4csyd.onion/.
DuckDuckGo onion
We review and list tools and products without bias, regardless of potential commissions. Purchases through links on our pages may yield affiliate revenue for us. Unfiltered engines Torch, Haystak, etc. will display everything, including scam sites or malware laced pages these are only as safe as your own caution. Engines like Ahmia, Not Evil, and those with filtering are safer in that they deliberately exclude some dangerous content, reducing the chance you’ll accidentally land somewhere bad. However, a VPN introduces its own trust factor you’re trusting the VPN not to log you, and it can slow down your connection further.
While the dark web itself isn’t illegal, several laws come into play depending on what’s being done. Choosing a dark web monitoring tool requires a lot of factors, including price, availability, and many other things. Lastly, keeping the Tor browser and any security software up to date is important for staying ahead of potential vulnerabilities.
- It's ideal for fast searching and doesn’t show cluttered results.
- In fact, Ahmia has a strict policy against abuse material it actively blocks things like child exploitation content from appearing in searches.
- Because of this, there’s no single dark web search engine that covers everything comprehensively.
- These sites are intentionally hidden to protect the privacy and anonymity of both the site operators and visitors.
- I’ve used it to jumpstart research, like a 2024 privacy guide that needed reliable .onion links fast.
Engines like Ahmia minimize this with no-log policies, but misconfigurations (e.g., enabled plugins) or correlated metadata can expose users. These newcomers focus on user trust and cross-network support (e.g., I2P), but verify their .onion stability via communities. Yes, OnionLand supports image and video searches on .onion sites, pulling from indexed media with suggestions for refined queries. The dark web subset demands higher security due to potential illicit content, making specialized tools essential. Verify by cross-checking links with directories like tor.taxi or r/onions, checking site uptime via Ahmia’s stats, and avoiding JavaScript-enabled pages.
Not really; some, like Ahmia, will filter harmful or illegal content, while others will just serve you unfiltered results with possibly dangerous links. They exist on the .onion domain, accessed via the Tor browser (or similar tools). Even though using a good search engine is what everyone wishes for, don’t ever forget that you must hide yourself very well on the internet to avoid criminals.
How To Access onion Sites Safely
The proliferation of IoT and 5G devices will provide new attack vectors for infostealer gangs. Their tools often spread through phishing campaigns or compromised software downloads, enabling crimes such as identity theft. In 2025, state-sponsored actors are expected to continue using the dark web for politically motivated cyberattacks.
By staying alert, verifying sources carefully, and consistently practicing good security habits, you significantly reduce the risk of encountering threats or compromising your security. While exploring the dark web can offer valuable privacy benefits, it’s crucial to understand common risks and how to manage them effectively. Follow these straightforward steps to set up Tor and begin searching safely. You’ve probably heard of the “dark web” and wondered what exactly it is and how people navigate its hidden corners. Radar Rundown Free firewall software allow privacy ethusuiasts to secure their network and block mal… Radar Rundown Darknet markets are anonymous platforms on the dark web for trading illegal goods usin…
Navigating Results Safely
Torch’s philosophy is to provide broad access and let the user beware. This means anything goes in the results you might see links to disturbing content or obvious scams. So think of it as Google like searching, but over Tor without Google monitoring you. DuckDuckGo is not a dark web specific engine, but it’s hugely popular on Tor for general searching. But for 90% of use cases finding onion sites related to your topic Ahmia is an excellent first stop.
- But we highly recommend you switch to torgol as soon as possible for better privacy and search experience
- Secondly, it’s not just a search engine, but also has a links’ directory and a stumbler.
- Meaning, if you search for “credit card shop from Netherlands”, only those sites which contain all of these words will be shown.
- It will make your VPN activities seem like normal traffic, so you can use an uncensored internet.
- Because it is so unrestricted, Excavator is best suited for advanced threat intelligence analysts.
The Z-Library functions as an intricate network of hundreds of interconnected web domains and is available through TOR and I2P platforms. Users can also view individual profiles of vendors and marketplaces, providing information such as ratings, alternate links, the number of listings, and the percentage of uptime. It’s important to differentiate between genuine search results and paid placements.
If someone’s caught buying or selling illegal items like credit card numbers or hacked data, they can face serious federal charges—even if it all happened behind an anonymous screen. That said, a significant chunk of U.S.-based activity on the dark web still revolves around illegal marketplaces—selling things like stolen data, counterfeit documents, and even drugs. In the U.S., dark web usage has been growing steadily—not just among cybercriminals, but also among privacy-conscious users.



