The Australian Federal Police (AFP) participated in a Europol-led investigation that in 2024 shut down LockBit’s primary platform along with 34 servers across the US, the UK, Europe, and Australia. Continuous monitoring of stealer logs, credential leaks, and dark web chatter should be a core function of threat intelligence, not an occasional sweep after an incident. Gizmodo may earn a commission when you buy through links on the site. The editorial team did not participate in the creation of this guide. If you manage not to expose your private information and avoid illicit activities, you can be sure everything will be okay.
What Is A Cloud Access Security Broker?
Just bypass your standard web browsers and fire up your tor browser to get on the dark web to access one of the best tor sites. Without further ado, let’s take a look at some of the best tor and onion links for you to check out, in no particular order. Detractors argue that online anonymity encourages criminality and impedes law enforcement. The Tor network also gave hackers, terrorists, and distributors of illegal pornography a secure method of communication. The earliest form of the modern dark web arose in March 2000 when Irish student Ian Clarke developed and released Freenet, which offers anonymous communication online via a decentralized network of Freenet’s users. Naiyie is a former content strategist at CyberGhost, where she researches and writes about cybersecurity and tech-related topics.

TorBook aims to be a privacy-focused alternative to mainstream social networks. I found it especially useful for testing new services without risking my main email address, though messages expire after 24 hours. I found their technical explanations clear and well-researched, though the site updates less frequently than other news platforms. My testing showed it loads quickly and offers the same high-quality content as its regular website, making it an excellent resource for readers in censored regions. ProPublica provides Pulitzer Prize-winning uncensored investigative journalism through its .onion service. I especially like how TorLinks categorizes links based on their type, letting you easily find what you need.
What Can I Do If My Personal Information Is On The Dark Web?

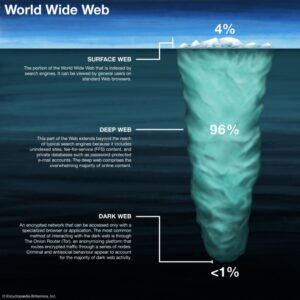
It specialized in narcotics fentanyl, heroin, cocaine, stolen financial data, fake documents, and even in house money laundering/mixing services. In practice, authorities combine blockchain forensics, metadata analysis and international raids to dismantle these sites. Unlike the deep web private or unindexed pages, the dark web specifically refers to sites requiring special software Tor to access. In 2026, dark web websites frequently change domains and are often short-lived. What’s the difference between classic marketplaces and data stores? Launched in September 2022, Torzon Market operates on the Tor network and features over 11,600 illegal products, including drugs and hacking tools.
Dark Web Sites Offering Educational Resources
DuckDuckGo is a search engine that prioritizes user privacy, distinguishing itself from competitors by not tracking search history or personal information. Categories might include but are not limited to, secure communication services, marketplaces, financial services, and whistleblowing sites. The Hidden Wiki categorizes links under several headings, making it easier for users to find what they're looking for. This assortment reflects the diversity of content available beyond the reach of standard internet browsing, including both legitimate resources and those of a more dubious nature. Accessed through the Tor network, a privacy-focused browser that anonymizes user's web traffic, The Hidden Wiki operates as a directory service.
Types Of Dark Web Websites

Initial access brokers (IABs) are thriving, selling entry points into corporate environments, which are then monetized by ransomware affiliates or data extortion groups. Under the cloak of anonymity, cybercriminals and threat actors can operate, selling an array of tools and services that can be used to wreak havoc on organizations. Tor is a Firefox-based browser made specifically to enable access to onion sites, hence the name The Onion Router. Unlike the surface web, the dark web is a part of the internet not indexed by conventional search engines. Initially designed for secure military communications, it evolved into a broader tool for online anonymity, later expanding to public use with the Tor network.
Dark Web Links For News
Such sites include blogs, gaming sites, social media, and super-encrypted email platforms. People who live under a government that deeply supervises or censors internet traffic eventually get attracted to the dark web. As much as the Darknet contains even the “good” stuff, it’s not a place you need to stumble about blindly without proper dark web safety. According to recent research, Bitcoin tumblers are increasingly used for money laundering. The attacks have led to the formation of other cybercriminal groups and Cyber Extortion.
What Is The Dark Web & How To Access It Safely In 2025
When you search for something on Google or Bing, you’re using the clear web. The Dark Web is a hidden part of the internet, completely different from the clear web we all use daily. Then I’ll explain how to enter dark web websites.
Is It Illegal To Visit Dark Web Websites?
- Which dark web browser did you use to visit sites on the dark web?
- ProtonMail is an email service that uses end-to-end encryption, making your email accessible to you and only you.
- Silk Road was one of the first dark web marketplaces and it allowed users to trade multiple types of nefarious goods and services, including weapons and identity fraud resources.
- It’s a space where anonymity is paramount, and it operates outside the reach of traditional search engines like Google or Bing.
- Although the underground internet world is rife with everything bad, it also hosts positive elements.
- With these in mind, let’s take a closer look at the dark web sites rundown.
The biggest difference is that the Tor website encrypts users’ internet traffic and anonymizes their connection. The onion site is especially beneficial for people in regions with heavy censorship or restricted access to media. The Tor Browser can take you to all kinds of questionable, dangerous, and potentially illegal content. So take this guide as you explore where to go on the Tor Browser without risking your online security. The Hidden Wiki and its mirrors and forks hold some of the largest directories of content at any given time. Media coverage typically reports on the dark web in two ways; detailing the power and freedom of speech the dark web allows people to express, or more commonly reaffirms the illegality and fear of its contents, such as computer hackers.
The Hidden Wiki
People often have bad feelings about the dark web, but not everything on it is illegal or dangerous. Tor Browser already comes with HTTPS-Only mode, NoScript, and other patches to protect your privacy and security. Torch is the oldest dark web search engine and it has no restrictions when it comes to search engine results. However, if you want unfiltered and uncensored search results you can try Torch.
Used ethically, such as for privacy or study, one can search this area lawfully and safely. By encrypting communication before it gets to the Tor network, pairing Tor with a VPN gives a second degree of protection. Research of the dark web is legal as long as national or international laws are not broken. Indeed, most nations; including the United States, the United Kingdom, and India, allow access to the dark web as a lawful activity. Access to ".onion" domains and anonymous surfing made possible by specialised software like the Tor Browser allows entry only.
It’s fragmenting into specialized communities that include credential marketplaces, exploit exchanges for zero-days, malware kits, and access to compromised systems, and forums for fraud tools. But the pace at which takedowns occur, the evolution of the threat actors will continue to outpace law enforcement capabilities,” Kroll says. Nonetheless, takedowns usually result in valuable threat-intelligence grabs that benefit the cybersecurity community and intelligence that cannot be obtained anywhere else. These peer-to-peer, invite-only, and/or vouchering networks are faster, cheaper, and less vulnerable to disruption by law enforcement,” Kroll says. “Some migrate to private forums, other ransomware groups, create new ransomware groups, or adopt decentralized technologies like blockchain-based hosting or intermittent access platforms that are harder to trace and takedown. The group provided bulletproof hosting (BPH) services to the cybercriminals that breached health insurer Medibank Private.
That’s why it’s never a good idea to burn Tails on DVD. When you’re done surfing or shopping on the dark web, don’t forget to shut down Tails. Still, if you’re really itching to purchase a new phone or God knows whatever, I would advise you to stick with Bitcoins or your favorite crypto coin.
If you are familiar with Quora and Reddit, Hidden Answers is the dark web’s version for its users. When you access this site, do so with extra protection, even if you are technically anonymous when you use the Tor browser. People like spies or whistleblowers often contact the CIA via the dark web to keep themselves hidden.