“Until a few years ago, criminals managed to get a lot of credit card information from POS terminals—anywhere you used your card to swipe it,” says Ziv Mador, vice president of security research at Trustwave. “There is underground trade in stolen personal information, account information, and financial information” on the dark web, says Danny Rogers, co-founder and chief executive officer at Terbium Labs, an information security startup. Cybercriminals "have been known to purchase expired payment cards to gain more information on potential victims," notes the threat intelligence company Cyble in a post about the leak.
Navigating The Rising Tide Of AI Attacks
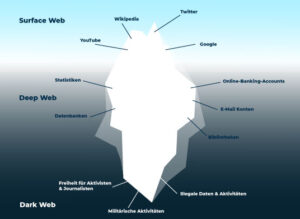
There are entire websites, channels, and forums dedicated specifically to carding. Contrary to popular belief, most carding platforms no longer hide in the dark web (i.e. the Tor network). There’s an underground ecosystem where sensitive data is bought, sold, and traded—not just on the dark web, as you might expect, but also on publicly accessible websites, channels, and forums. The offers on the site do not represent all available financial services, companies, or products. Your lender or insurer may use a different FICO® Score than FICO® Score 8, or another type of credit score altogether.
Under federal law, a credit card user’s liability generally may be limited to $50 if they report the fraud within 60 days. You may not notice your credit card has been compromised until it gets declined or you start receiving monthly bills for transactions you never authorized. We will also share some effective safety tips and discuss how virtual cards can help protect you from card fraud. When it comes to credit card fraud, the best offense is a strong defense.
Types Of Credit Card Hacking
Redline malware was the most widespread infostealer, accounting for some 34% of all infections across 2024, but the biggest surge came from Risepro which saw its share increase from just 1.4% in 2023 to 23% in 2024. Criminal marketplaces on the dark web, only accessible by way of a special web browser and often by invite only depending on the forum concerned, are selling full access to small businesses for $600 and access to insanely valuable healthcare data for $1,000 a pop. Judging from the activity on the shop, BidenCash appears to be thriving in 2023, providing an active data and money exchange platform in a market that has experienced a decline in recent years. However, it's noteworthy that this recent release lacks the comprehensive data quality that previously set BidenCash apart.

Criminals Are Selling Millions Of Stolen Credit And Debit Card Numbers On The Dark Web
One compromised payment processor or e-commerce platform can yield thousands of card numbers at once. What many don’t realize is that much of this stolen data comes from large-scale breaches rather than individual card skimming. Sellers often provide buyers with validity rates for their data and even offer replacements for cards that don’t work. The pricing varies based on the card type, with premium cards from certain banks fetching higher prices.
Conducting transactions online while connected to an unsecured WiFi network places your financial data at risk of being stolen due to MITM attacks. Credit card skimmers are devices that threat actors use to steal your credit card information. You can also share your virtual card details with family members without revealing your underlying bank information. While the virtual card is tied to your real account, the merchant or a potential hacker can't access your actual bank details. Millions of customers’ card data have been compromised in the past decade.
How A PayPal Account Or Credit Card Ends Up On The Dark Web
Many tracker apps link directly to bank accounts for up-to-the-minute info. Tracker apps offer a powerful way to keep tabs on credit card activity. Spotting fraud on your accounts is key. This makes it crucial to monitor accounts closely and use strong security measures.
Phishing Scams
Our guide will help you recognize payment card vulnerabilities and stay on guard. Credit card theft has become one of the most common types of fraud, with the U.S. projected to lose a staggering $165 billion in the coming 10 years due to card abuse. Cyberthreats are constantly evolving, and your security measures should be continuously updated as well.
Data Sheets
Reporting the incident can help the bank work with law enforcement to find the perpetrator. You should notify your bank immediately if you find any suspicious activity. In 1984, a significant data breach occurred involving TRW and Sears. The breach highlighted the need for increased security measures, including two-factor authentication and regular system updates. There are some dark web monitoring services that include financial checks, but these are mostly subscription based.
Kaspersky SD-WAN Introduces New Hardware And Software Enhancements To Improve Network Performance
- The 2014 Home Depot data breach was a massive attack that compromised 56 million credit cards.
- Since the dark web provides its users with anonymity, cybercriminals often use it to carry out criminal activities like trafficking stolen personal information and selling illegal weapons.
- Stolen card data is being leveraged in many ways on the dark web, adds Rogers.
- Their members trafficked over 1.7 million credit cards in less than three years.
Criminals use stolen credit card data to make unauthorized transactions, purchase illegal goods, or fund other illegal activities. With this stolen information, fraudsters can make unauthorized purchases, withdraw funds, or even create counterfeit credit cards. Criminals use stolen credit card information to make unauthorized transactions and drain victims' accounts. Cybercriminals exploit vulnerabilities in payment systems, compromising credit card details.
This Threads account was created on September 28, five days after Pavel Durov’s post stating that his team had “made Telegram Search much safer” by removing content from users trying to “sell illegal goods.” One particularly large account that we are tracking has 12.4K followers; the account’s bio contains a link back to a Telegram channel with an even larger number of members. Modern loyalty solutions integrated mobile payments, rewards and ecommerce technology to get customers to keep coming back. By Sumit Arora, Senior Vice President, Enterprise Payments Strategy, Wells Fargo Building a Balance Between Competition and Collaboration There is a long history between banking and technology, dating back to around 1866 when the telegraph .
Second batch in recent months likely came via online theft, reports Group-IB Users now need an exact channel name or link to surface some of these channels, instead of being able to search key fraud-related terms and return all of the public channels with those terms in their names and descriptions. While we have seen an increase in deactivations of Telegram channels discussing illicit topics, the vast majority of channels discussing fraud, scams, malware, hacking, and cybercrime that we track continue to exist on the platform. We actively monitor Telegram and were able to independently confirm what appears to be increased content moderation in the form of removing or deactivating channels used to discuss fraud and cybercrime.
Credit card fraud on the dark web operates quite differently from what many people imagine. Service providers play a critical role in the broader financial security ecosystem, so one of the most valuable things you can do is empower your customers with clear, practical advice. Even in regions like the EU, where banks are legally required to implement strong customer authentication, criminals continue to find ways to bypass these safeguards. Carding has long been a prevalent form of online crime—and it remains a serious threat.

Your credit card number is a valuable piece of data for cybercriminals. One of the most common items sold on the dark web is stolen financial information, including credit card numbers. If your card information has been compromised, it could lead to unauthorized charges, identity theft, or even drained bank accounts. Large-scale data breaches at retailers, financial institutions or other companies can expose millions of customers' credit card numbers to hackers.
This stolen information is exploited by threat actors for financial gain through unauthorized charges, account takeover, and identity theft. Checkers are tools used by individuals and organizations to verify the validity and authenticity of credit card information and are used by threat actors to check the illicit information they purchase. According to the Nilson Report, the cost of credit card fraud worldwide in 2024 stands at a staggering $35.79 billion , and it is projected to eclipse over $40 billion by 2026. These cards are then used by cybercriminals to make online purchases, including buying gift cards, that are hard to track back to them. Point-of-sale card skimmers, targeted Magecart attacks on websites and info-stealing trojans are among their top tools for stealing credit-card data. A dump of hundreds of thousands of active accounts is aimed at promoting AllWorld.Cards, a recently launched cybercriminal site for selling payment credentials online.

How Technology Is Evolving To Counter Card Fraud On The Dark Web
- Contrary to popular belief, most carding platforms no longer hide in the dark web (i.e. the Tor network).
- Credit cards, Paypal accounts, and fullz are the most popular types of stolen information traded on the dark web, but they’re far from the only data worth stealing.
- • Stolen card data prices ranged from $17 to $120 in 2022
- The validity of cards obtained through phishing can vary; however, they often demonstrate a relatively high validity rate due to several factors.
- Attackers posted the stolen data for sale on Joker’s Stash, a dark web marketplace that exclusively trades stolen card data.
Staying alert to suspicious activity can protect your finances. These alerts can spot fraud fast and keep your money safe. Credit card safety requires active steps. AVS systems also catch fake online buys. Flare and other smart tech can track stolen info. Check bank statements often for odd charges.