However, many activities conducted on the dark web – such as accessing illegal marketplaces, purchasing illicit goods or services, or participating in criminal activities – are absolutely illegal. However, after it became accessible to the public, criminals and extremists began using it for illegal activities. The most popular type of software is called Tor (which stands for “The Onion Router” as all the sites in the dark web end in .onion instead of .com). These dark web sites are unsearchable to the general public.
Parents Text Content
“Some of those arrested not only uploaded and watched videos but also abused children,” Europol said, while confirming that “the investigation is ongoing,” making it appear likely that more arrests could follow. KidFlix going dark was the result of the biggest child sexual exploitation operation in Europol’s history, the agency said. Europol seized the servers and found a total of 91,000 unique videos depicting child abuse, “many of which were previously unknown to law enforcement,” the agency said in a press release. Some of those arrested not only uploaded and watched videos – but also abused children themselves. ‘Of course the real danger zone for pornographic material is the dark web where extreme and illegal material proliferates and there is frighteningly easy access.’

Notable Dark Web Search Engines
(e) The search engine directs CSAM-seekers to self-help websites and asks them to complete our survey. (b) Our web crawlers collected online content from 176,683 different onion domains from 2018 to 2023. These sexual preferences are classified as mental health disorders because they result in self-harm and harm to others, and therapy can improve well-being and prevent harm to children5. A large portion of this group is likely to have sexual interest in children (i.e., paedophilia or hebephilia)4.
Practitioners who work with men with sexual offences may therefore face individuals whose sexual offences occurred partly or wholly in the darknet. Since 2008, access to the darknet has been facilitated by the The Onion Router (TOR) browser, bringing the darknet within reach of an increasingly wider audience. By routing traffic through a random combination of servers worldwide, the darknet obfuscates the identity of its users, making it an attractive medium for journalists, dissidents, and individuals committing crimes. Police also arrested a “serial” child abuser in the US, CBS News reported. Suspects were typically people who had been on the darknet for a long time.

Reporting The Truth Restoring The Church
Furthermore, there are real CSAM websites that do not use explicit sexual language and instead refer to content such as ‘baby love videos’. We randomly select the plain text representations of 1000 onion websites for each year, 2018–2023, and read the text content of these websites to determine whether they share CSAM and what the English vocabulary is for this type of page. These websites host a variety of content, and there are Tor-specific search engines for searching. In 2020, an article published in The Proceedings of the National Academy of Sciences (PNAS) acknowledged that ‘The Tor anonymity network allows users to protect their privacy and circumvent censorship restrictions but also shields those distributing child abuse content14’. ’ presents an online survey of 517 Tor users where several users are concerned about CSAM; however, this does not lead to any further analysis in the paper, and it avoids mentioning child abuse12.
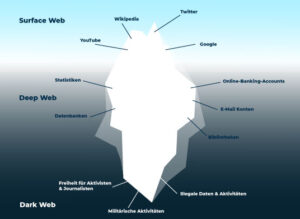
Increased risks for children and adolescents reaching the dark web during the COVID-19 pandemic are multiple14 and include online grooming for various purposes, introduction to suicide, and child pornography.7 Child pornographic content is shared among offenders who redistribute them online through the dark web, causing lifelong harm to the victims.7 The Onion Router, launched in 2002, uses the principle of onion routing, developed at the United States Naval Research Laboratory in the 1990s, in which the user data are first encrypted and then transferred through different relays present in the network.12 Thus, it creates multilayered encryption (like layers of an onion) and keeps the identity of the user safe. Although not all content in the dark web is illegal, more than 60% of the sites on the dark web host illicit material.9 The term dark web indicates the set of publicly accessible contents that are hosted on websites whose IP address is hidden, but can be accessed by using dedicated software, as long as they know the address (Table I; available at ).
Some companies behind AI image generators have attempted to fight malicious content by restricting thousands of keywords, but ActiveFence’s report indicated that users of dark web pedophile forums trade guides spelling out how to work around keyword restrictions and other safeguards. These images aren’t just spreading on the dark web, either, but on “social media, public forums, or pornographic websites,” the FBI warned. Earlier this month, the FBI issued an alert, “warning the public of malicious actors creating synthetic content (commonly referred to as ‘deepfakes’) by manipulating benign photographs or videos to target victims,” including reports of “minor children and non-consenting adults, whose photos or videos were altered into explicit content.” Normally, content of known victims can be blocked by child safety tools that hash reported images and detect when they are reshared to block uploads on online platforms. Federal prosecutors say the website, Welcome To Video, was run by 23-year-old Jong Woo Son on the “darknet,” a section of the internet known for its more complicated infrastructure, user anonymity and lack of easy access. He said McIntosh mostly oversaw the site’s fantasy and roleplay rooms, where “sick people engage in a game” of pretend sexual abuse.
Aiming To “Bring Healing,” Angelina O’Mara Speaks Out For The First Time Behind Bars
Finally, inactive members were once full or registered members, but have failed to meet the requirements set by the forum to maintain their membership status. Registered members have begun the process of registering on the forum but have yet to meet other requirements of membership. Full members have registered on the forum and meet all other requirements of membership, such as, for instance, a minimum number of posts to forum threads. Depending on forum policy, “full members,” “registered members,” and “inactive members” can be distinguished.
- On the darknet, once a transaction has been processed, merchants cleverly conceal, package and ship the product out using everyday shipping services like the US Post Office, UPS or FedEx.
- In addition to contributing child pornography, he advised users on ways to avoid detection by law enforcement.
- However, technological advancements such as encryption and privacy-focused browsers like Tor enabled the general public to access it.
- "Despite increased moderation, predators continue to target minors on your platform," Warner wrote.
- It's something built into the password management services offered by Apple and Google as well, so you don't need to trawl through data leaks manually yourself.
Facebook announced in March plans to encrypt Messenger, which last year was responsible for nearly 12 million of the 18.4 million worldwide reports of child sexual abuse material, according to people familiar with the reports. Until laws are clear on how society should deal with child sexual exploitation deepfakes, it seems that the obscene AI images will keep spreading, potentially increasing demand while AI tools potentially get trained on more illegal images that users keep uploading. Children whose photos were used were harmed, Gagnon said, as well as children harmed by the growing market for such AI content and any children victimized by anyone whose “fantasies” were “fueled” by the flood of AI images normalizing illegal activity online. The Post reported that in the past few months, NCMEC has fielded “a sharp uptick of reports of AI-generated images,” as well as more “reports of people uploading images of child sexual abuse into the AI tools in hopes of generating more.” Clear intervention pathways should also be established to deter the onset or perpetuation of CSAM offending, thus enabling law enforcement to focus on those forum members who pose the greatest risk to children and who encourage cognitive distortions of forum users. The access to technology and a connected community via the Internet has enabled the distribution, possession, and creation of child sexual abuse material (CSAM) to increase.
“AI Child Sexual Abuse Imagery Is Not A Future Risk – It Is A Current And Accelerating Crisis”

Our search engine at GOTDW is here to help you explore more safely, but we still urge extra caution as you dive in. Whether you're curious about the hidden corners of the internet or need practical tips on navigating it, we are here for you. Get on the Dark Web (GOTDW) is your go-to guide and safe search engine for exploring the dark web responsibly.

In the US, there has been at least one recent case where creating “sexually explicit ‘deepfaked’ images” of minors resulted in criminal charges. The agency pointed to hashing resources like Take It Down, operated by the National Center for Missing and Exploited Children (NCMEC), to report content and have it removed—but that won’t block any AI-generated images that could be created next by AI tools potentially trained on the image. Some tools, like Stable Diffusion, seemingly rely on open source tools that can make images generated by the tool harder to track and police online, the Post reported.
Uncover the threats that are relevant to you by leveraging Lunar’s continuous monitoring of the deep and dark web. Designed for cybersecurity teams, Lunar enables advanced threat detection, credential leakage monitoring, actor profiling, and tactical intelligence extraction—at scale and in real time. Members exchange tips on using compromised credit cards, highlight recent data dumps, and discuss market-related updates.
Top 5 Data Removal Services Of 2025
If the person targeted is 18 or over, you can submit the content to StopNCII.org, a project operated by the Revenge Porn Helpline and dedicated to supporting take-down efforts. If the person targeted is under 18, report the material to the National Center for Missing and Exploited Children’s (NCMEC) CyberTipline. In total, 16 subject matter experts from across the child safety ecosystem were identified and consulted during this phase. Research methods were designed to identify respondents’ perceptions and experiences related to deepfake nude imagery. Without these interventions, the spread of deepfake nudes will continue to outpace efforts to control the misuse of generative AI for these purposes, further normalizing the creation and distribution of nonconsensual content at scale.
Child Sexual Abuse Material In The Digital Age

These are real children who have appeared in confirmed sexual abuse imagery, whose faces and bodies have been built into AI models designed to reproduce new imagery of these children. It's a place where you'll find data leaks and illegal trades, but also legitimate, legal online activities users want to carry out without attracting the attention of law enforcement agencies or governments. When asked how they learned about the websites, platforms, or apps they used to create the content, deepfake nude creators described multiple, highly accessible pathways. The data on young deepfake creators explored in this section should be viewed as directional, underscoring the urgent need for more nimble and comprehensive research on young people’s role in perpetrating this abuse. For young people, technology can intersect with sexual exploration and romance, with many reporting experiences of sharing nudes with a romantic partner or visiting websites containing adult material (such as dating or pornography sites).
Teens And The Darknet
Its mission of open access is debated within academic and publishing communities. It contains millions of scientific research documents from around the world. Sci-Hub is a massive database that eliminates the barriers to getting scientific knowledge. The website is available on the surface web and has a .onion site. It aims to expose abuses of power and betrayal of public trust through investigative journalism. ProPublica is a popular online publication that won five Pulitzers in 2016.
Research conducted in 2015 found there were 900 child sexual abuse forums like “Boystown” active on the darknet at the time, together receiving an average of 168,152 requests per day (Owen and Savage 2015). Its members find vulnerable children online, elicit private information and intimate sexual images from them, and then use that sensitive material to blackmail victims into mutilating themselves or taking other violent action — all while streaming it on social media so others can watch and torment the victims too. More than nine in ten people in the UK say they are concerned at how images and videos of children being sexually abused are shared through end-to-end encrypted (E2EE) messaging services. Politicians, law enforcement, regulators and all those responsible for protecting children must work together to ensure that the technology is properly regulated, and AI-generated sexual images of children are removed as a top priority.
Deep Web Radio
You can use DuckDuckGo on the dark web if you’re looking for a search engine that works like Google. Wonderful overall highlights of the TOR, DarkWeb and some useful sites. Aside from being a place for legitimate research and activities, the dark web is home to the world’s most nefarious black markets. The Tor Project is a nonprofit organization, it started as a university research project. It’s just a tiny part of the overall internet and its links are not indexed in central registries.