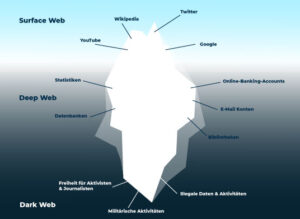
As mentioned above, some common use cases for the deep web include accessing paid subscriptions and online accounts. The surface web is anything on the internet that you’re able to search for on standard search engines like Google. The deep web, also known as the hidden web, is the part of the internet where almost all online activity happens. Google searches optimize websites based upon the indexation rule. The anonymous part of the internet and Deep Web segment that conventional Google search engines cannot optimize is called the Dark Web. Normally, search engines will not turn up these types of search results if you try to access them.
Reconnoitre – Open-Source Reconnaissance And Service Enumeration Tool

Attackers buy these credentials to gain initial access to corporate networks and cloud environments, often for just a few dollars per account. This includes customer data, financial records, intellectual property, and internal communications that were never meant to be public. The real danger for organizations isn't the dark web itself, but how cybercriminals use it as a marketplace for stolen data and attack tools. This creates a direct connection between your organization's security posture and the underground economy.
What Are The Best Browsers For The Deep Web And The Dark Web?
- If you want to access the Dark Web, follow the security measures pointed out in this blog to be safe and anonymous while reaching out.
- This structure benefits data protection, as financial records or research data stay confidential, but it complicates access for authorised parties.
- The content is generally more secure and clean than that of the surface web.
- From a cyber-security perspective, it can be if you don’t know how to protect yourself.
- The deep web hosts a variety of content necessary for everyday activities that require privacy and security, such as email accounts, subscription services, paywalled content, and private business databases.
People buy and sell illicit goods and services, share illegal files, sell criminal services, and carry out cybercrime, hate crimes, stalking, and more. However, the dark web’s anonymity makes it a breeding ground for criminal activities. Company data that businesses store internally to manage operations and consumer data from inputted forms belong to the deep web. These parts of the unindexed internet serve very different purposes.
Still, it is critically important to never share any info about yourself with the people you meet and not purchase anything. Additionally, using robust anti-malware software is another way of staying safe. Pay close attention to the data permissions you authorize, which means you don’t want to click “yes” each time a popup appears on a website asking for it. However, if you’re determined to access the dark web, there are several steps you should take to protect yourself.
Security Threats
You can’t open Chrome and expect to find any dark web pages via a Google search. Most of the internet you're familiar with is likely covered under this definition. Take these steps for better search results, including adding my work at Lifehacker as a preferred source.

The Technology Behind The Deep And Dark Web
If you want to access the dark web, you need special tools to do so. But unlike the latter, the dark web is not accessible via a typical web browser like Chrome or Firefox. If you access your YouTube account's settings page, that's the deep web. In your daily life online, you frequently jump between the surface web and the deep web, likely without realizing it. Sure, you’ll find Netflix via a Google search, but you won’t find the player for Love Is Blind, Season 9, Episode 1 unless you log into the site first.

For one, it underscores the importance of being vigilant about internet security and privacy. The existence of the dark web and the deep web has important implications for internet users. Finally, the dark web and the deep web also differ in terms of the level of anonymity they provide to users. There are several key differences between the dark web and the deep web that are important for internet users to understand. While it is true that the dark web is often used by criminals to conduct illegal activities, law enforcement agencies around the world are actively working to combat these activities. For example, websites like WikiLeaks have used the dark web to publish classified documents that expose government corruption and human rights abuses.
Deep Vs Dark Web: 17 Critical Differences
Once it bypasses these layers, you get access to the content available on the dark web. What makes the dark web different is that it can't be accessed with your everyday web browser — this anonymous and decentralized portion of the internet requires a special browser. It's basically anything you can't find or access through a Google search. So they're right there on the internet, but you can't find them by doing a quick search. But below the surface lies the deep web — the parts of the internet that aren't indexed. In fact, Statista reported there were 5.35 billion internet users as of January 2024.
Best Practices For Browsing The Deep And Dark Web Safely
However, depending on the systems and software involved, authentication can be very complex to implement, and errors in implementation can undermine the purpose entirely. Authentication is much better at preventing unauthorized access to resources. The unfortunate disadvantage is that the obscurity itself is illusory, and growing more so everyday, giving those who depend on it a false sense of security about their assets.

What Is The Difference Between Deep Web, Darknet, And Dark Web?
Accessing the Dark Web requires special tools like Tor (The Onion Router), a software that anonymizes internet traffic and allows users to remain untraceable. Unlike the rest of the Deep Web, the Dark Web often features illegal or contentious content, making it a focus of interest and concern among regulators and law enforcement. This exposure can lead to legal repercussions if law enforcement tracks illegal activities back to you, despite the anonymity. Phishing sites or malware can be used to gain access to your login credentials potentially leading to data theft or account takeover. While it’s best known for underground markets, drug sales, and hacking services, it also hosts legitimate content. People use it daily when accessing personal accounts or cloud storage.
This type of scam is incredibly prevalent on the Dark Web, making it extremely easy for criminals to defraud people. Due to the anonymity of the seller and buyer, these marketplaces are full of fraudulent sellers. Transactions on these illicit marketplaces are made using cryptocurrencies to maintain user anonymity. These marketplaces use .onion domains and are accessible only through the Tor browser. Although it is hard for the police to catch criminals who use Tor to conceal their activities, occasional slipups and errors by those criminals expose them. This is why they carefully monitor the dark web and dark web marketplaces.

Unlike the dark web, which requires specialized browsers, deep web content often exists on the regular internet but remains inaccessible without proper authentication or direct links. Business operations requiring confidentiality, credential-protected services, internal corporate systems, and regulatory compliance with data protection requirements That said, participating in illegal online activities is a crime.
For this reason, all the access data must be indexed through any search engine. Just because a page cannot be accessed by search engines doesn’t mean it’s trying to promote illicit activity. It covers a range of content that is not accessible by web search engines like Google, Safari, or DuckDuckGo. The deep web is the part of the internet you can’t access through search engines like Google and Bing.
What Kind Of Content Can You Find On The Deep Web?
The Deep Web is the realm housing an extensive collection of information that the average internet user cannot access using standard search engines. It includes all the content not indexed by standard search engines such as Google or Bing. With the Deep Web, if you’re accessing personal accounts or sensitive data, the primary risks are related to security and privacy breaches. The Dark Web is a hidden portion of the internet that can only be accessed through specialized software like Tor or I2P. The Deep Web makes up the majority of the internet, far surpassing the size of the Surface Web, which includes all publicly accessible websites. While the surface web is easily accessible through Google or other search engines, the Deep Web includes any content that requires special access.