Law enforcement agencies worldwide have grappled with the challenges posed by the Dark Web, attempting to balance the need for online privacy with the necessity of combating criminal activities. The U.S. Naval Research Laboratory developed the precursor to the Tor (The Onion Router) project during this period as a means to protect government communications. The concept of an encrypted, hidden layer of the internet began taking shape in the 1990s. The dark web is notorious for hosting a wide range of cyber threats that pose significant risks to individuals and organizations. Other search engines like Haystak boast millions of indexed pages and advanced filtering options.

How To Use Tor Browser Safely

Later released as open-source, it became widely accessible for privacy-focused use. It works by routing your encrypted traffic through multiple volunteer-operated servers, known as onion routers. Tor, short for The Onion Router, is a privacy-focused network that allows you to browse the Internet anonymously.
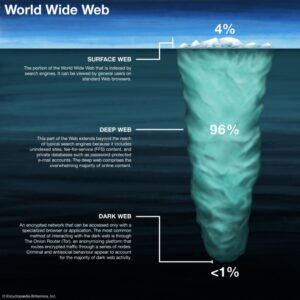
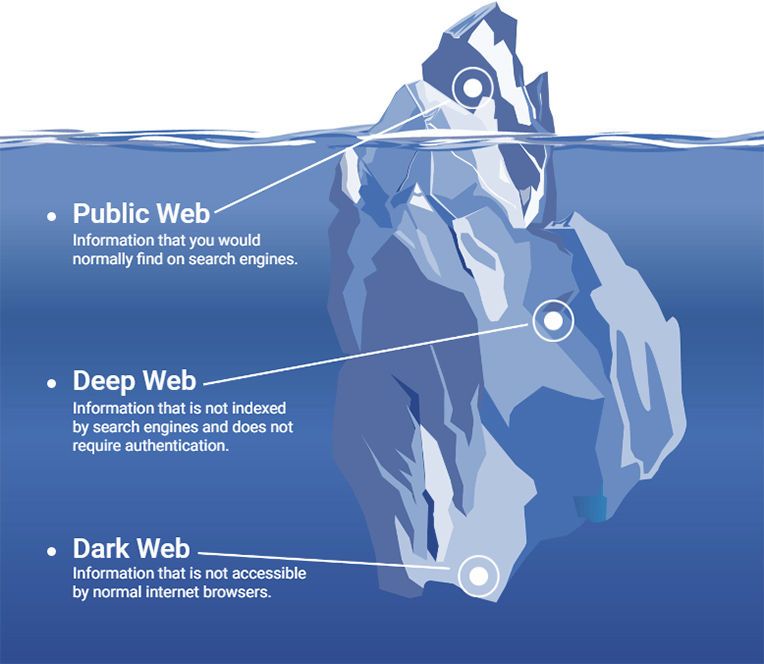
Beneath it lies the deep web and, further still, the dark web – a hidden network often shrouded in mystery, speculation and misinformation. We believe everyone should be able to explore the internet with privacy.We are the Tor Project, a 501(c)(3) US nonprofit.We advance human rights and defend your privacy online through free software and open networks. With Tor Browser, you are free to access sites your home network may have blocked.
Why Can’t You Use Google On The Dark Web?
Initially, the dark web was mainly used by government agencies, big businesses, hackers, and cybercriminals. Note that most dark web transactions are carried out using Bitcoin or other cryptocurrencies. It relies on P2P connections and requires specialized tools and software. As a result, you cannot find them with a regular search engine. Some of the deep web sites do not use standard top-level domains (TLD) such as .gov, .com, .net, etc. You can find sites like Facebook, Wikipedia, e-commerce sites, YouTube, and more here.
The Dark Web
Automated actions isolate compromised systems and secure access to critical assets, reducing risk exposures. The platform records detailed cloud workload telemetry using Storylines technology. SentinelOne’s agentless CNAPP provides KSPM, CSPM, AI-SPM, and EASM features to assess vulnerabilities in cloud workloads, IT infrastructures, and services. Additionally, SentinelOne can identify sensitive data and assets within your organization, leveraging its AI-powered threat intelligence to prevent potential data breaches.
- In this guide, we’ll cover the dark web access guide, explain how to use Tor browser safely, and answer key questions like is it safe to browse the dark web.
- That’s how Tor works, making it nearly impossible to track users.
- Though the dark web hosts illegal activities and malicious sites, it also serves legitimate purposes like secure communication for activists and journalists.
- Through the dark web, private computer networks can communicate and conduct business anonymously without divulging identifying information, such as a user's location.
- Many email services, citing security reasons, require a phone number for identity verification.
- Whenever a data breach occurs, the information will likely end up on the dark web for sale.
This dark web monitoring will help you track illicit activities and minimize the risks of cyber-attacks. If you get a reliable vendor, you should procure the services to stay safe when accessing the dark web. Many dark net sites do not undertake the necessary measures to protect users like most websites on the surface web. For example, the Silk Road site operator, an illegal dark web marketplace, was traced and arrested. Because of this, some people use it to get around government restrictions, while others use it for illegal activities like smuggling drugs and weapons.
How Do You Access The Dark Web Safely?
During my tests, ExpressVPN’s military-grade encryption and verified no-logs policy provided consistent protection against tracking and monitoring. Pitch is a dark web-based Twitter/X alternative, providing a secure platform for anonymous discussions and information sharing. TorBook aims to be a privacy-focused alternative to mainstream social networks. I found it especially useful for testing new services without risking my main email address, though messages expire after 24 hours. Alt Address provides disposable email addresses specifically designed for dark web use.
We’ll also discuss why it’s dangerous and why you should inform yourself about the dark web even if you don’t plan to be on it. The sharing of illegal pornography and discussion of illegal sex acts account for a significant portion of dark web traffic. Not all mass thefts of data facilitated by the dark web have been motivated by money. In March 2012 Russian hacker Yevgeniy Nikulin and three accomplices stole passwords for 117 million e-mail addresses from the social media company LinkedIn and then offered the data for sale on the dark web. The rise of cryptocurrency, and in particular Bitcoin, significantly increased the dark web’s use in illegal trade.
The dark web is rife with cybercriminals who offer their services either as individuals or as part of a group. Fraudulent activities on the dark web include phishing scams, fake identity sales, and the sale of fake products. Carding refers to the theft and illegal use of credit card information, and the dark web offers a platform for criminals to sell and buy such information.

Most reliable gateway to the dark web is the Tor Browser. Access to ".onion" domains and anonymous surfing made possible by specialised software like the Tor Browser allows entry only. And remember—on the internet, what you don’t see can still hurt you. Understanding the Dark Web isn’t about fear—it’s about awareness. However, for every journalist using it for security, there are 100 hackers using it to exploit victims.
What Is The Dark Web? How Safe Is It And How To Access It? Your Questions Answered
- Despite the negative aspects, there are many people today who utilize the dark web for good, legal reasons.
- It’s a hidden layer of the internet beyond the reach of traditional search engines.
- The dark web, by contrast, is configured on darknets — online networks that can be accessed only with special software and techniques.
- The dark web is home to the internet’s hidden sites, services, and products — some innocent, others downright dangerous.
Using a Virtual Private Network (VPN) adds an extra layer of security. While Tor provides anonymity, it doesn’t hide the fact that you’re using Tor. It’s a free, open-source browser based on Firefox that is pre-configured to connect to the Tor network. If you’re curious about exploring the dark web for legitimate reasons, safety should be your top priority. For those living under authoritarian rule, the dark web provides a vital tool for dissent. The motivations for using the dark web are diverse, ranging from noble causes to criminal enterprises.
By investing in dark web monitoring tools, training staff, and implementing cybersecurity best practices. These are pages and services that aren’t indexed by search engines, but they’re not hidden or secret — just restricted. The dark web is often used to bypass censorship and access restricted content in countries with heavy internet control, like China and Russia. “.Onion” sites are specifically designed to keep traffic and data private, which means they’re blocked from being found by regular search engines.
How Can You Access The Dark Web Safely?
National Security Agency (NSA) contractor Edward Snowden, who was concerned about the extent of government surveillance, used Tor to coordinate with journalists on leaking 1.5 million classified government documents. Credit card and social security numbers are routinely purchased, as are passwords for e-mail accounts—sometimes en masse. In addition to traditionally forbidden trade, the dark web became a hub for the sale of stolen information. The U.S. Federal Bureau of Investigation (FBI) arrested Ulbricht in October 2013, but imitators still arise, many much larger. In February 2011 Ross Ulbricht founded what is believed to be the dark web’s first black market, Silk Road.

Others may act in ways that are illegal for the protection and safety of others. When viewed through this lens, the dark web’s legality is based on how you as a user engage with it. But of course, these benefits can be easily extended to those that want to act outside of the constraints of laws in other explicitly illegal ways. Understanding that the nature of the internet meant a lack of privacy, an early version of Tor was created to hide spy communications. The dark web was once the province of hackers, law enforcement officers, and cybercriminals. When it comes to dark web safety, the deep web dangers are very different from dark web dangers.
What Activities Are Considered Illegal?
For day-to-day use, a VPN provides a high level of privacy while also having minimal effect on your internet experience. A major drawback of all dark webs is that they are very slow. Whistleblowers, journalists, and other professionals at risk of targeted surveillance use the dark web to communicate sensitive information.
Webpages on the open web will show up in search results on sites like Google and Bing. Tech researcher and writer with a passion for cybersecurity. Discovering that your personal data is circulating on the dark web is akin to a personal violation. After more than a year of no updates, the site admin shut it down, reasoning that he couldn’t keep the list of onion links up-to-date.
“This shift complicates law enforcement’s ability to track illicit financial flows, pushing agencies to invest in new blockchain forensic tools and cross-chain analytics,” Kurrie says. Increasingly, privacy-focused coins such as Monero (XMR) and Zcash (ZEC) are being adopted to protect anonymity and make tracing funds difficult for law enforcement. There are also reports of “evil GPT” products sold on dark forums or via private messaging, according to Vishavjit Singh, senior threat intelligence researcher at eSentire. Generative AI is being used to fabricate synthetic identities, including deepfake voices, forged credentials, and AI-generated backstories. In one case, the Rhadamanthys stealer developer explicitly states they want purchasers to crypt the malware, with posts from the developer highlighting partnerships with crypting services.