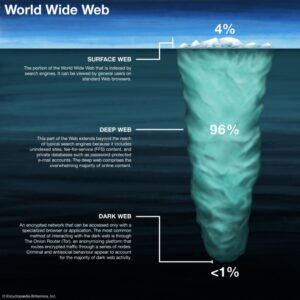
This just involves turning on your VPN before you open Tor and connect to dark web sites. It’s, ironically, more conspicuous than using popular browsers and sites. Since all activity on the dark web is anonymous by default, it is definitely where the murkiest transactions on the internet take place. To look at it in a different way, it makes up between 90% and 95% of the internet.
While Tor lets you reach .onion sites, many require invitations, passwords, or verification. Many people use it for privacy-focused communication, whistleblowing, or accessing restricted information in censorship-heavy regions. The dark web is not exclusively used for illegal activities.
How To Stay Safe On The Dark Web?
- An easy way to find content on the dark web is to receive a link from someone who already knows about it.
- Therefore, you should stay cautious and avoid clicking when accessing the dark web.
- It is designed to ensure user anonymity while offering access to a diverse array of information available on the dark web.
- The websites on the dark web have the domain name ‘.onion’ as part of their URL.
- ’, the first thing that comes to mind are criminal activities, ranging from hired hackers to an online drug market.
In this sequel, I’m going to show you some of the not-so-clear-web’s hidden Easter eggs and how to get there. Upgrade your lifestyleDigital Trends helps readers keep tabs on the fast-paced world of tech with all the latest news, fun product reviews, insightful editorials, and one-of-a-kind sneak peeks. Microsoft Word is one of our favorite word processors because it's versatile and lets you craft simple documents or wonderful stories with ease.
With DuckDuckGo, you can view dark web websites because, unlike regular search engines, it can index .onion websites. Unlike regular search engines such as Google, Yahoo, Bing, DuckDuckGo does not store your data, ensuring complete anonymity. However, make sure you’re careful which links you click on — some of them lead to sites that contain illegal content and services.
Even if a person does not make any purchases on illegal marketplaces like the Silk Road, custom software used by law officials can analyze activity and identify user identities. However, some of these alleged services, such as professional ‘hitmen,’ may be scams designed to defraud willing customers. You can find almost every kind of computer virus and malware on the dark web, which is why it’s a primary source for spreading these digital threats. However, researchers believe most of them could only be scams. Interestingly, darknet sites also offer stolen documents and passports from around the globe. The information can be of any kind, either social security numbers or even bank card numbers (the bank/credit card information is usually sold in bulk).
Subscribe To The Blog Newsletter
You can access it with regular web browsers and search engines. It means you cannot access websites on the dark web with regular browsers like Firefox or Chrome. The dark web is part of the internet that is not indexed by standard search engines like Google, Yahoo, and Bing. As such, we do not recommend using Tor if you want to do data-intensive activities like streaming in HD, gaming, torrenting, or making video calls. The anonymity provided by onion routing comes at the cost of slowing your internet considerably. Many reputable websites and news outlets like ProPublica and SecureDrop often share official domain addresses of onion sites on their pages.
Is It Legal To Access Dark Websites?
However, extra caution is advised—use a good VPN and ensure the security settings of your device are up to date to minimize risks. Download and install Tor first, and optionally a VPN for added security. The dark web is accessed with the help of special software like the Tor Browser. It is used for anonymous messaging, secure data transfer, and communication of information. SentinelOne’s integrated identity protection safeguards defend against Active Directory and Entra ID attacks, stopping dark web-driven phishing and credentials theft. Automated actions isolate compromised systems and secure access to critical assets, reducing risk exposures.
Myth 4: The Dark Web Is Inherently Dangerous To Visit
In addition, you can connect your Keybase account with X, GitHub, or Reddit to let people easily trust that they are talking to the actual person. To increase the security level, add password protection and determine the expiration time for messages. It protects their submissions using high-end encryption and doesn’t log their IP addresses or device information – full anonymity.
It also always uses a secure HTTPS connection, so you’re safer on public Wi-Fi networks too. One of its best features is Anonymous View, which is a free proxy that masks your identity while you’re browsing sites. Plus, it lets you set your location for local results, manage safe search filtering, and there’s even an AI “Assist” tool that provides AI search results — so you don’t have to visit web pages to find your answer. And I liked that if I visited a site that had a .onion version, it prompted me to switch to that version.
What Are Onion Sites?
This includes email accounts, private databases, paywalled sites, and subscription services. Your activities on the dark web are not entirely shielded from tracking, and relying solely on anonymity can lead to a false sense of security. It’s not illegal per se to access an onion website, but that doesn’t mean your actions while connected to the dark web are immune from law enforcement. Anonymity of the dark web is one of the main draws for using onion sites, and most dark web links use a “.onion” domain.
Top 10 Dark Web Search Engines In 2026 (Tools For Staying Anonymous On The Dark Web)
- So, you risk being flagged or investigated for visiting certain sites, even without criminal intent.
- Now that you’ve completed the download, it’s time to install the Tor browser on your device.
- Yes, you can access the dark web on a smartphone, but you’ll need an appropriate browser, like Tor browser for Android or Onion browser for iPhone.
- Users should always be cautious about where they explore, as some spaces can hold harmful or troubling content.
- The dark internet is designed to provide anonymity by keeping communication private through encryption and routing online content through multiple web servers.
Yes, via apps like Tor Browser for Android or Onion Browser for iOS, but desktops offer more security. A VPN combined with Tor provides better anonymity. We’ll focus on secure, ethical practices tailored to cybersecurity professionals and IT leaders.
Google Feud
The VPN is a second layer of extra protection, on top of the protection that the Tor network already offers. Obviously not all Tor users, but you never know whether someone might be looking into you. It’s not a secret that ISPs (Internet Service Providers) and the FBI are tracking Tor users. It’s important to arm yourself with a good VPN (Virtual Private Network) when you want to enter the dark web to protect your privacy and anonymity. So, to get into the Tor network, follow the steps I’ve listed below.
That means that only 0.024% of all the known pages are findable in Google’s search engine. Hypothetically speaking, Google may be aware of well over 200 trillion individual pages (these are obviously NOT all indexed in the search engine). This was also Google’s latest official update on how many pages are in their database.
How To Access The Dark Web Safely: A Step-by-step Guide
The dark web is infamous as a dangerous place, where drugs are bought and hitmen hired, but it can be a safe way to browse the internet if your privacy is serious concern. “Try ITarian free and streamline IT operations—cloud ticketing, remote access, and patch management with zero setup cost” Have you ever opened a laptop or connected a new monitor and wondered why everything looks blurry, o… Every 39 seconds, a cyberattack occurs on the internet. Have you ever needed to run a system command, check network settings, or troubleshoot software issue… Ever needed to install new security software or troubleshoot compatibility issues and wondered, “h…