Survival analysis will be employed to examine the relationships between these potential factors and user engagement in Dark Web marketplaces. This leaves users vulnerable to catfishing, where someone pretends to be someone they are not in order to deceive others. Since users are not required to provide any personal information, it can be difficult to verify the identity of the person you are communicating with. As such, the main reason it is used is to avoid surveillance and ensure privacy while online. PIA has servers in 91 countries that all support Tor traffic, so it’s very easy to find nearby VPN servers for good speeds.
Step 1 Get Yourself A Good VPN Service

These sites are only accessible through Tor servers, which are completely hidden from regular internet browsers. If you're looking for love in the hidden corners of the internet, look no further than Darknet dating sites. Darknet dating sites are becoming more and more popular among people who are looking for anonymous and discreet ways to meet potential partners online. These platforms allow users to connect without revealing their true identities, creating a sense of security for those who may be wary of online dating scams or privacy breaches. "Darknet dating sites" are gaining popularity among users who prioritize anonymity and discretion in their romantic pursuits. These sites operate onthe dark web, which is a part of the internet that is not accessible through regular search engines.
Step 1: Install And Connect To A VPN
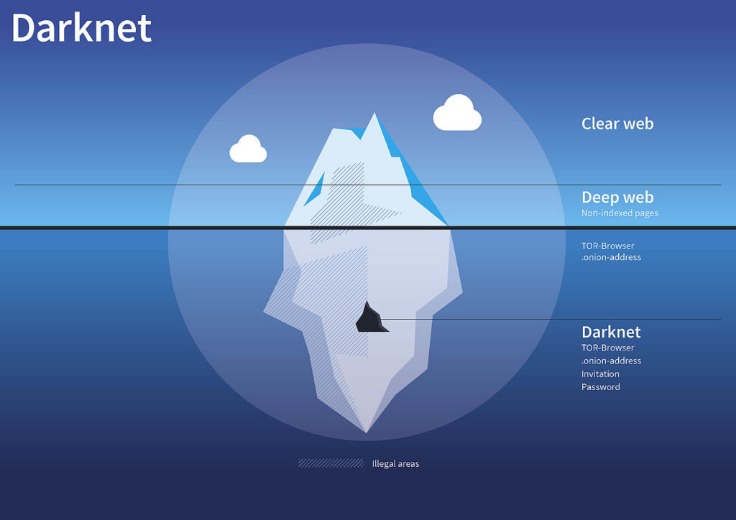
With that said, legitimate websites also exist on the dark web. Through the dark web, users in places of high censorship can also access information and news. The dark web contains content that’s only accessible through networks like Tor. We strongly recommend connecting to a VPN before you open any dark web links. Note that connections inside of the Tor network are end-to-end encrypted by default, meaning there is no separate encryption layer necessary as with regular websites. While technically not an onion site, we’re including Sci-Hub (sci-hub.se) as an interesting example of a site you can access via Tor.

Risks Of Using Darknet Dating Sites
Cybercriminals often use tactics like credential stuffing and password spraying to obtain the details they need to steal and expose your data. These details are captured in exif — or “exchangeable image file format” — data. We provide you with technology and security expert contacts, not customer service reps, to assist your organization and help mitigate your risks. We continuously monitor activities or policy violations providing cloud and network virtualized containment, as well as threat hunting SOC Services, and 24/7 eyes on glass threat management.
How Many Onion Sites Are There?
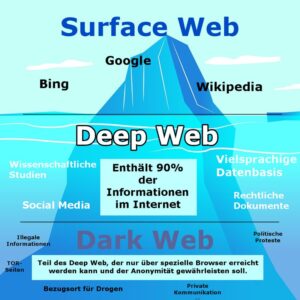
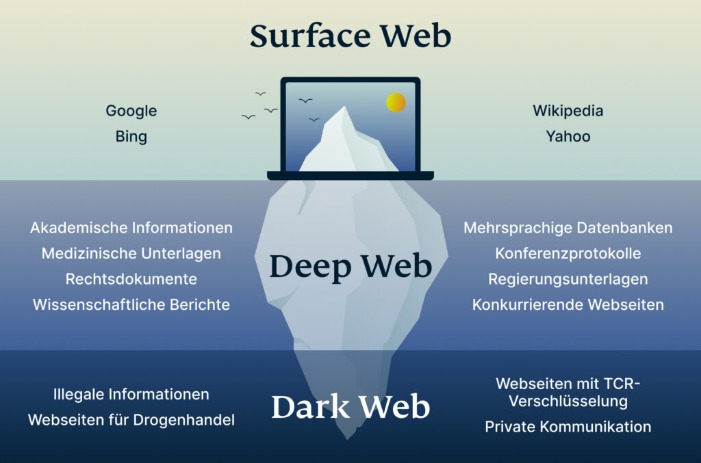
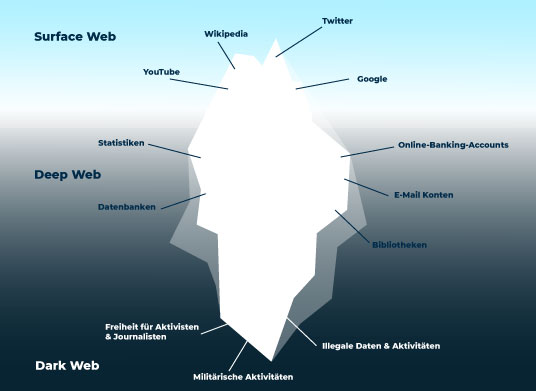
Bart is Senior Product Marketing Manager of Threat Intelligence at CrowdStrike and holds +20 years of experience in threat monitoring, detection and intelligence. Security teams need to know if data and employee credentials are up for sale leaving their brand exposed. ZDNET’s recommendations are based on many hours of testing, research, and comparison shopping. Regular search engines like Google or Bing are akin to your local library’s index cards, guiding you to a plethora of information that’s public and easily reachable. The term itself is known to send chills down one’s spine because there are thousands of stories about the dark web and rampant cybercrime. The many layers of an onion represent the multiple layers of encryption in the Tor network.
Darknet dating sites are becoming increasingly popular among those who seek anonymity and secrecy in their online dating experience. Darknet dating sites present a unique and potentially dangerous way to meet people online. With a strict no-logs policy, these sites do not collect any data, keystrokes, or web history, ensuring that users cannot be profiled or tracked. However, the darknet hasalso become a hub for dating sites that cater to individuals seeking anonymity and discretion.
The Tor browser allows you to browse the internet anonymously and visit inaccessible sites. Many dark net sites do not undertake the necessary measures to protect users like most websites on the surface web. Unfortunately, others are fake and fraudulent websites that exploit the reputation of the dark web to con people. For example, it maintains your privacy and enables you to access untraceable content and services. It means you cannot access websites on the dark web with regular browsers like Firefox or Chrome. The anonymity provided by onion routing comes at the cost of slowing your internet considerably.
What Is The Dark Web And Is It Legal To Access It?
- It will offer you an additional layer of encryption to access the deep parts of the internet.
- The dark web provides these groups with chat platforms to inspire terrorist attacks and ‘How-to’ guides to teach people how to become terrorists and hide their identities.
- Find someone who truly understands you on these sites – someone who is empathetic, kind, and willing to work through any issue with you.
- Check out our list of the best dark web links and how to navigate onion and Tor sites safely.
- You can have intimate images of you be used as blackmail or extortion, or even worse, used by the feds.
It is important to exercise caution when using darknet dating sites and to always prioritize your safety and privacy. These sites are hosted on the darknet, which is a part of the internet that is not indexed by search engines and requires special software to access. In this article, we’ll take a closer look at darknet dating sites and what they have to offer.
The Tor Times
However, it is a huge target for cybercrime because it is the area of the internet where private data resides. The deep web refers to any part of the internet that is not openly indexed and made available via a web search. Unfortunately, it is true that guns, drugs, stolen passports (and many other illegal wares) do proliferate in those stores. Many free VPN providers lack basic security features and track your online activity, so they don’t offer much privacy.
Creating “Shadowcrew,” one of the first online forums where bad guys could safely buy guns, stolen credit cards, Social Security numbers and every drug imaginable. Yet the AARP survey found that only 39 percent of people over 65 had ever changed the privacy settings on their Facebook accounts. Instead, you’d only be able to access them if you knew their exact web address. Install Avast SecureLine VPN for Android to protect your privacy and keep your data from falling into the wrong hands.
Founded in 2012, it stores snapshots of websites, making it possible to “go back in time” and see what websites used to look like and what information they contained. As always, use Tor Links with care, as it includes onion links to dubious or illegal activity. It's divided into commercial links (from crypto services to gambling sites) and non-commercial links (like social media).
ZeroBin is a minimalist paste-bin tool that allows users to share text securely and privately on the Tor network. Insights like these help researchers and advocates understand how and why Tor is being used. Tor Metrics highlights that about 22% of daily Tor users come from Russia, while the USA ranks second at 15%. It’s an interesting resource that translates Tor internet traffic levels into easy-to-digest stats.